Comparing Offline Solutions
by Natural Born Prepper

1 Introduction
 This document will describe Prepper Offline in detail, and provide a white paper on why Prepper Offline is the best solution for offline knowledge resilience, along with a comparison of Knowledge Resilient Distributed Architectures.
This document will describe Prepper Offline in detail, and provide a white paper on why Prepper Offline is the best solution for offline knowledge resilience, along with a comparison of Knowledge Resilient Distributed Architectures.
It explores the growing dependency on centralized, cloud-based information systems and highlights the risks associated with losing access to critical knowledge when it is needed most.
In an increasingly digital world, access—not ownership—has become the defining factor of value, and this document challenges that assumption by reframing knowledge as a form of durable, portable wealth.
At its core, Prepper Offline is presented as a self-contained, distributed knowledge system designed to function independently of internet connectivity. Unlike traditional online platforms, which rely on continuous access to external infrastructure, Prepper Offline enables users to download, store, and replicate a complete preparedness library across multiple devices and locations.

This architecture removes single points of failure and ensures that vital information—ranging from survival skills and food storage to medical guidance and communication strategies—remains accessible under any conditions.
The document also provides a structured comparison between different approaches to storing and accessing knowledge, including cloud-based systems, static document collections, hardware-dependent solutions, and distributed offline libraries.
Through this comparison, it becomes clear that systems relying on centralized infrastructure or single devices introduce significant risk, while distributed, file-based architectures offer greater resilience, redundancy, and long-term reliability.
Prepper Offline stands out by combining structured organization, advanced search capabilities, and full portability into a single, cohesive system.
Ultimately, this white paper positions Prepper Offline not just as a product, but as a strategic shift in how individuals think about preparedness. By treating knowledge as an asset that must be secured, duplicated, and made available without dependency on external systems, users can achieve a higher level of self-reliance and readiness.
In this sense, Prepper Offline is not simply a library—it is a resilient knowledge infrastructure built for real-world uncertainty.
2 Knowledge as a Survival Asset
2.1 The Shift from Digital Wealth to Knowledge Resilience
 At first glance, knowledge does not appear to carry the same weight as wealth. It is not measured in balances, stored in accounts, or tracked in markets. Yet in any disruption—whether economic, technological, or environmental—knowledge becomes one of the most valuable assets a person can possess.
At first glance, knowledge does not appear to carry the same weight as wealth. It is not measured in balances, stored in accounts, or tracked in markets. Yet in any disruption—whether economic, technological, or environmental—knowledge becomes one of the most valuable assets a person can possess.
This shift mirrors what we see in digital wealth systems. Just as cryptocurrency represents a move away from traditional financial structures, modern preparedness is moving away from reliance on centralized information systems. The difference is subtle but critical. In the same way that preppers question the stability of banks, currencies, and financial institutions, they must also question the systems that store and deliver knowledge.
Today, most information exists in digital form. It lives in:
- Websites
- Cloud platforms
- Online communities
- Streaming and search-based systems
This creates the illusion that knowledge is always available. It feels permanent, searchable, and instantly accessible. But like digital wealth, this availability is conditional. It depends on infrastructure, systems, and assumptions that are rarely examined.
The shift toward knowledge resilience begins with recognizing that information is no longer something you simply “have access to.” It is something you must intentionally secure, store, and preserve—just like any other critical resource.
For preppers, this represents a change in mindset.
Instead of asking:
- “Where can I find this information?”
The more relevant question becomes:
- “Do I control access to this information when I need it?”
This is the foundation of knowledge resilience.
2.2 Why Information Access Is a Critical Dependency
In modern systems, access to information is often taken for granted. Search engines provide answers instantly. Tutorials, guides, and expertise are available on demand. This convenience has fundamentally changed how people interact with knowledge.
But convenience introduces dependency.
The ability to access information today relies on multiple layers:
- Functional devices
- Power availability
- Internet connectivity
- Platform accessibility
- Continued existence of the source
Each of these layers represents a potential point of failure. Under normal conditions, they operate seamlessly, reinforcing the belief that information is always within reach. However, when even one layer fails, access can be disrupted.
This creates a critical distinction:
Information can exist without being accessible.
A guide, a manual, or a piece of knowledge may still exist somewhere in the world, but if you cannot retrieve it when needed, it has no practical value in that moment.
This dependency becomes more significant in high-stress or time-sensitive situations. When decisions must be made quickly—how to purify water, treat an injury, secure a location—there is no margin for delay or uncertainty. The system must work immediately, or it does not work at all.
From a preparedness perspective, this transforms information from a passive resource into an active requirement. It must be:
- Available
- Accessible
- Usable without delay
The modern reliance on digital systems has shifted knowledge from something people carry internally to something they retrieve externally. This outsourcing of knowledge increases efficiency—but reduces resilience.
The risk is not that information disappears.
The risk is that access disappears at the moment it is needed most.
2.3 Applying “Digital Wealth Fragility” to Knowledge Systems
The same principles that define digital wealth fragility apply directly to knowledge systems.
In Digital Wealth, Fragile Foundations, wealth is not treated as something inherently stable. Instead, it is understood as a system-dependent construct—one that requires continuous functionality across multiple layers to remain usable. The same is true for knowledge stored in digital environments.
Knowledge systems today share many of the same characteristics as digital financial systems:
- They are abstract rather than physical
- They depend on infrastructure
- They rely on software and interfaces
- They require user interaction and understanding
This creates similar vulnerabilities.
For example, an online knowledge platform may appear robust, but its accessibility depends on:
- Servers remaining operational
- Network connectivity being intact
- Access permissions being maintained
- The platform continuing to exist
If any of these conditions fail, access is interrupted.
This mirrors the structure of digital wealth systems, where value depends on:
- Network operation
- Cryptographic integrity
- Software compatibility
- Infrastructure stability
In both cases, the underlying asset—whether value or knowledge—exists within a system. And in both cases, that system introduces dependency.
Different offline solutions attempt to reduce these dependencies in different ways.
Some systems reduce external dependency but introduce concentration risk:
- Hardware-based systems rely on a single physical device
- Failure of that device can eliminate access entirely
Other systems distribute information but introduce complexity:
- Large PDF collections may lack structure
- Search and retrieval may become inefficient
More resilient models focus on distribution and replication:
- Files can be copied across multiple devices
- Access is not tied to a single system
- Failure of one instance does not eliminate access
The key insight is that:
Every knowledge system has an architecture—and every architecture has failure points.
2.4 Core Thesis: Access Defines Value
At the center of this document is a principle that directly parallels the core doctrine of digital wealth:
If you cannot access it, you do not own it.
This applies equally to knowledge.
A library that cannot be opened, a file that cannot be read, or a system that cannot be accessed does not provide value—regardless of the amount of information it contains. Value is not determined by existence alone. It is determined by usability at the moment it is required.
This leads to a critical reframing of how knowledge systems should be evaluated.
Instead of asking:
- “How much information does this system contain?”
The more relevant question becomes:
- “Can this system reliably deliver the information when I need it, under any condition?”
This shifts the focus from quantity to accessibility.
In this context, different solutions reveal different strengths and weaknesses:
- Centralized systems offer scale but depend on infrastructure
- Hardware systems offer control but introduce single points of failure
- Fragmented systems offer flexibility but reduce usability
- Distributed systems offer resilience through replication
This is the distinction that defines value in preparedness systems.
Value is not static.
Value is conditional.
It depends on:
- Access
- Reliability
- Simplicity
- Redundancy
From a prepper perspective, this leads to a clear doctrine:
Knowledge must be treated like any other critical resource.
It must be secured, duplicated, and made accessible under adverse conditions.
Because in the end:
Information you cannot access is no different than information you never had.
3 The Architecture of Offline Knowledge Systems
3.1 What Defines an “Offline Solution”
 At a surface level, the concept of an “offline solution” appears simple. It suggests that information can be accessed without an internet connection. However, this definition is incomplete. True offline capability is not just the absence of internet dependency—it is the absence of external dependency at the moment of use.
At a surface level, the concept of an “offline solution” appears simple. It suggests that information can be accessed without an internet connection. However, this definition is incomplete. True offline capability is not just the absence of internet dependency—it is the absence of external dependency at the moment of use.
Many systems marketed as “offline” still rely on hidden assumptions. They may require specific software, functional hardware, or prior setup conditions that are rarely considered. These hidden dependencies only become visible when systems are stressed or fail.
A true offline knowledge system must operate independently of external infrastructure. It must not rely on remote servers, live authentication, or real-time connectivity. More importantly, it must function predictably under degraded conditions.
To properly define an offline solution, it is necessary to consider what it does not require.
A resilient offline system should not depend on:
- Internet connectivity
- External servers or cloud services
- Continuous updates to remain functional
- Specialized or proprietary access environments
Instead, it should rely on what is locally controlled and immediately available.
This distinction becomes critical when evaluating preparedness systems. A solution that functions offline under ideal conditions but fails under degraded conditions is not truly resilient. It is simply disconnected, not independent.
The difference between disconnection and independence defines the quality of an offline system.
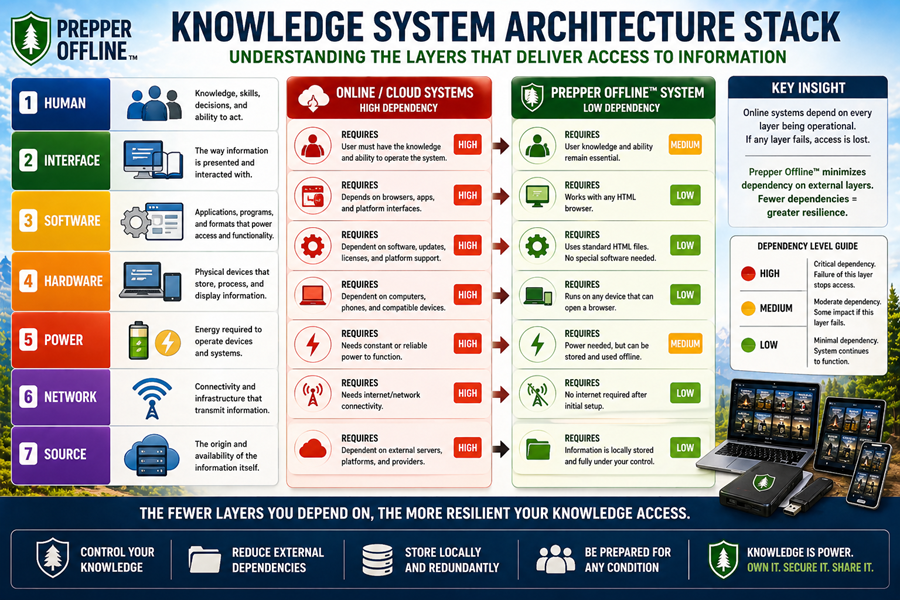
3.2 Layers of Dependency (Hardware, Software, Access, Human)
Every knowledge system, whether digital or physical, is built on layers. These layers form the architecture that determines how information is stored, accessed, and used. Understanding these layers is essential because each introduces its own dependencies and potential failure points.
At a minimum, most knowledge systems rely on four core layers:
- Hardware
- Software
- Access interface
- Human interaction
Each layer must function correctly for the system to deliver value.
Hardware represents the physical foundation. This includes devices such as computers, storage drives, servers, or printed materials. Hardware failure can immediately render a system inaccessible, regardless of how well the information is stored.
Software introduces another layer of dependency. File formats, operating systems, and applications determine whether information can be interpreted. A file that cannot be opened is effectively lost, even if it still exists.
The access interface defines how users interact with the system. This may be a browser, a reader, a search tool, or a physical indexing method. If the interface is too complex or fails under stress, access becomes inefficient or impossible.
Finally, the human layer is often overlooked. Systems that require training, familiarity, or specific workflows introduce cognitive dependency. Under stress, complexity becomes a failure point.
These layers can be summarized as follows:
- Hardware → Can the system physically function?
- Software → Can the data be interpreted?
- Interface → Can the user retrieve information efficiently?
- Human → Can the system be used under real conditions?
The more layers a system depends on, the greater its overall fragility. Each additional dependency increases the number of ways the system can fail.
Resilient systems reduce the number of required layers or simplify them to the point where failure is unlikely.
3.3 Access vs Ownership in Knowledge Systems
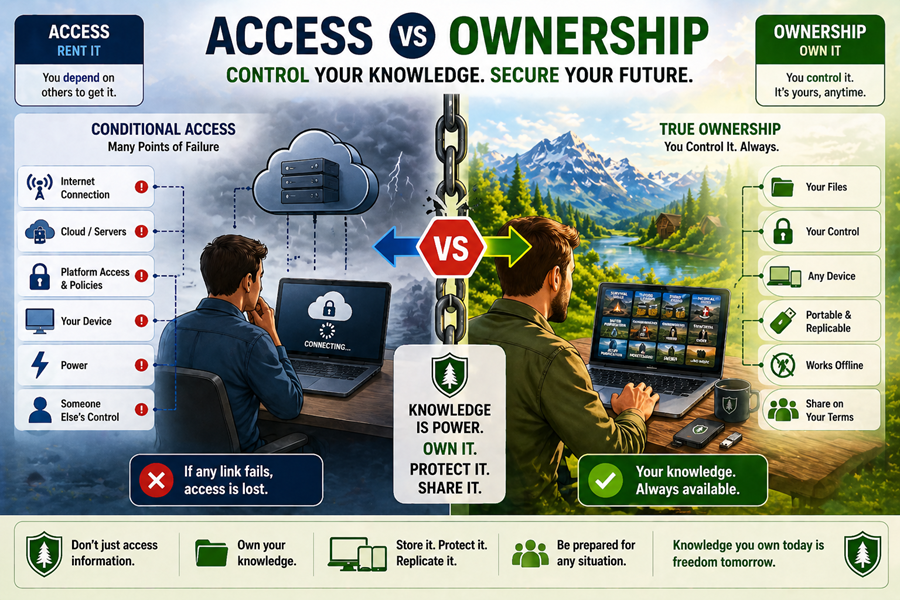 One of the most misunderstood aspects of modern knowledge systems is the difference between access and ownership.
One of the most misunderstood aspects of modern knowledge systems is the difference between access and ownership.
In digital environments, access is often mistaken for possession. Users believe they “have” information because they can retrieve it on demand. However, this access is frequently conditional. It depends on systems that are not controlled by the user.
This creates a false sense of security.
A person may rely on a website, a platform, or a digital library for critical knowledge. But if that system becomes unavailable, access disappears instantly. The knowledge was never truly owned—it was borrowed.
Ownership, in contrast, implies control.
A system that is owned allows the user to:
- Store information locally
- Access it without permission or authentication
- Duplicate and distribute it as needed
- Use it without dependency on external systems
This distinction mirrors the principles seen in digital wealth systems. Holding assets on an exchange provides access, but not true control. Similarly, relying on online knowledge platforms provides access, but not ownership.
Offline knowledge systems attempt to bridge this gap by moving information into environments that the user controls.
However, not all offline systems achieve true ownership.
Some still introduce constraints:
- Hardware-based systems concentrate ownership into a single device
- Fragmented systems make ownership difficult to manage
- Physical systems limit scalability and distribution
True ownership requires both control and usability. It is not enough to possess information—it must also be accessible under real-world conditions.
This reinforces a critical idea:
Ownership without access is not ownership.
3.4 Mapping Failure Points Across Architectures
Every knowledge system has an architecture, and every architecture contains failure points. These failure points define how a system behaves under stress and determine whether it remains usable when conditions degrade.
Failure points can exist at any layer of the system:
- Physical failure (hardware damage, loss, or destruction)
- Logical failure (corrupt files, incompatible formats)
- Access failure (inability to retrieve or locate information)
- System failure (dependency on unavailable infrastructure)
Different architectures concentrate or distribute these risks in different ways.
Centralized systems tend to concentrate risk. When knowledge is stored in a single location or device, that location becomes a critical point of failure. If it fails, the entire system fails.
Distributed systems reduce this risk by spreading information across multiple instances. In these systems, the failure of a single component does not eliminate access. Instead, redundancy ensures continuity.
However, distribution introduces its own challenges. Without proper structure and organization, distributed systems can become difficult to manage. Information may be duplicated inefficiently, or retrieval may become complex.
This creates a balance between concentration and distribution.
- Concentrated systems → Simpler, but higher risk
- Distributed systems → More resilient, but require structure
The goal of a resilient architecture is to minimize critical failure points while maintaining usability.
This requires:
- Reducing single points of failure
- Ensuring redundancy without excessive complexity
- Maintaining consistent access across different environments
From a preparedness perspective, failure is not a possibility—it is an expectation. Systems should not be designed for ideal conditions, but for degraded ones.
The architecture that performs best is not the one that works perfectly when everything is functioning. It is the one that continues to work when things begin to fail.
4 The Five Offline Models
4.1 Understanding the Landscape of Offline Knowledge Systems
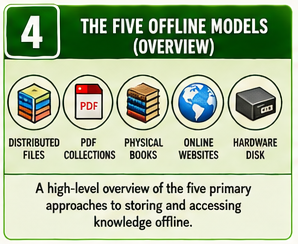 Not all offline solutions are created equally. While many systems are described as “offline,” they differ significantly in how they store, deliver, and protect knowledge. These differences are not just technical—they directly affect reliability, usability, and resilience under real-world conditions.
Not all offline solutions are created equally. While many systems are described as “offline,” they differ significantly in how they store, deliver, and protect knowledge. These differences are not just technical—they directly affect reliability, usability, and resilience under real-world conditions.
To properly evaluate offline knowledge systems, it is necessary to move beyond surface-level features and examine their underlying architecture. Each system represents a different approach to solving the same problem:
How do you ensure access to critical information when external systems are unavailable?
The five primary models represent distinct architectural approaches:
- File-based distributed systems
- Fragmented document collections
- Physical analog storage
- Cloud-dependent digital systems
- Hardware-based local servers
Each of these models introduces its own strengths and weaknesses. Some prioritize convenience, others prioritize durability, and some attempt to balance both. However, none are without trade-offs.
The purpose of this section is not to identify a single “best” solution, but to understand how each model behaves under stress. By examining their structure, dependencies, and failure points, it becomes possible to determine where each fits within a resilient preparedness strategy.
4.2 Prepper Offline™ — Distributed File-Based Architecture
Prepper Offline™ represents a file-based, distributed architecture designed to minimize dependency and maximize accessibility. At its core, it is a self-contained knowledge library that can be stored, copied, and accessed across multiple environments.
Unlike systems that rely on centralized infrastructure or specialized hardware, this model separates the knowledge from any single point of control. The entire system exists as a portable package that can be duplicated and distributed as needed.
This architecture provides several defining characteristics:
- The system is self-contained and does not require external connectivity
- It can be copied across multiple devices and storage media
- It uses standard browser-based access, reducing software dependency
- It supports redundancy through replication rather than centralization
This structure aligns closely with resilience principles seen in distributed systems. Instead of protecting a single instance, the system ensures survivability through duplication. If one copy fails, others remain available.
From a risk perspective, this reduces reliance on any individual component. There is no single device, server, or access point that determines availability. The system’s strength lies in its ability to exist in multiple places simultaneously.
This model mirrors the concept of decentralized control found in digital wealth systems, but without requiring active network participation. It achieves resilience through simplicity and replication rather than complexity and consensus.
4.3 PDF Collections — Fragmented Digital Architecture
PDF collections represent one of the most common forms of offline knowledge storage. They consist of individual documents gathered over time and stored locally. While they offer flexibility and ease of acquisition, they introduce structural limitations that affect usability and resilience.
Unlike unified systems, PDF collections are inherently fragmented. Each document exists independently, often without consistent organization, indexing, or navigation. This creates challenges when attempting to retrieve specific information quickly.
The architecture of this model is defined by:
- Independent files with no unified structure
- Reliance on external tools for viewing and searching
- Manual organization and categorization
- Limited integration between documents
While this approach allows for incremental growth, it also introduces complexity. As collections expand, managing and locating information becomes increasingly difficult.
From a dependency perspective, PDF collections rely on:
- Compatible software to open files
- Functional file systems for organization
- User knowledge to locate and interpret content
The primary risk is not loss of data, but loss of usability. Information may still exist, but the effort required to access it may exceed what is practical in time-sensitive situations.
This model parallels certain aspects of digital wealth storage where assets are technically secure but operationally difficult to manage. Without structure and accessibility, the value of the system is reduced.
4.4 Physical Books — Analog Knowledge Storage
Physical books represent the oldest and most established form of knowledge storage. Unlike digital systems, they exist entirely outside of technological infrastructure. They require no power, no software, and no network connectivity.
This independence provides a level of durability that digital systems cannot fully replicate. A book, once acquired, remains accessible as long as it is physically intact and available.
The architecture of this model is defined by:
- Fully offline, physical storage
- Direct human access without intermediaries
- No dependency on electronic systems
- Long-term durability under proper conditions
However, this resilience comes with trade-offs. Physical systems are inherently limited by:
- Storage capacity
- Physical space requirements
- Difficulty of duplication
- Limited search and retrieval speed
Unlike digital systems, scaling a physical library requires significant effort. Each additional copy must be physically produced and distributed. This limits the ability to replicate and distribute knowledge efficiently.
From a failure perspective, physical systems are vulnerable to:
- Environmental damage (fire, water, decay)
- Physical loss or displacement
- Limited redundancy unless intentionally duplicated
This model aligns closely with traditional hard assets in financial systems. Like gold or cash, physical books provide independence but lack flexibility and scalability.
4.5 Online Websites — Cloud-Dependent Knowledge Systems
Online knowledge platforms represent the most widely used method of accessing information today. They provide vast amounts of content, real-time updates, and advanced search capabilities. However, this convenience is built on a highly dependent architecture.
Unlike offline systems, online platforms rely on continuous connectivity and centralized infrastructure. The user does not control the system—only access to it.
The architecture of this model includes:
- Centralized servers hosting content
- Continuous internet connectivity
- Platform-controlled access and availability
- Dynamic, constantly updated information
This creates a system that is highly efficient under normal conditions but highly vulnerable under disruption.
The dependencies are significant:
- Power must be available
- Network connectivity must be stable
- Servers must remain operational
- Access permissions must be maintained
If any of these conditions fail, access is lost immediately.
This model closely parallels custodial digital wealth systems, where assets exist within a platform but are not directly controlled by the user. Access is conditional, and control is limited.
The primary risk is not degradation—it is total loss of access.
4.6 Hardware-Centric Architecture
Hardware centric architectures like Prepper Disk™ represents a hardware-based approach to offline knowledge storage. It consolidates information into a dedicated physical device, often designed to function as a local server or storage unit.
This model aims to combine the accessibility of digital systems with the independence of offline storage. By hosting content locally, it removes the need for external connectivity to the internet while maintaining a structured digital environment.
The architecture is defined by:
- A single hardware device acting as the storage and access point
- Local network or direct device access
- Integrated software environment for navigation and retrieval
- Centralized control within the device
While this approach provides a controlled environment, it introduces a critical risk: concentration.
All functionality depends on the continued operation of a single piece of hardware. If that device fails, access to the entire system is lost unless backups exist.
The dependencies include:
- Hardware reliability
- Power availability
- Device-specific software functionality
- Physical security of the device
This creates a single point of failure that must be managed through external redundancy.
From a conceptual standpoint, this model is similar to hardware wallets in digital wealth systems. It provides strong control and isolation but concentrates risk into one physical component.
4.7 Comparative Insight — Five Models, Five Architectures
Each of these models represents a different balance between convenience, control, and resilience. None are inherently perfect, and each introduces trade-offs that must be understood.
At a high level:
- Distributed file systems prioritize redundancy and replication
- Fragmented collections prioritize flexibility but reduce usability
- Physical systems prioritize independence but limit scalability
- Online systems prioritize convenience but depend on infrastructure
- Hardware systems prioritize control but introduce single-point risk
These differences are not just technical—they define how each system behaves under stress.
The key insight is that:
No system eliminates risk.
Each system redistributes it.
Understanding where that risk resides is the foundation of building a resilient knowledge strategy.
5 Prepper Offline™ — A Distributed File-Based Architecture
5.1 System Design: A Self-Contained, Replicable Knowledge Package
 Prepper Offline™ is built on a fundamentally different assumption than most knowledge systems: that access must not depend on any single system, device, or environment. Instead of centralizing knowledge, it packages it into a portable, self-contained format that can be replicated indefinitely.
Prepper Offline™ is built on a fundamentally different assumption than most knowledge systems: that access must not depend on any single system, device, or environment. Instead of centralizing knowledge, it packages it into a portable, self-contained format that can be replicated indefinitely.
At its core, the system is not an application, a platform, or a service. It is a collection of structured files designed to be accessed through universally available tools. This distinction is critical because it removes reliance on proprietary environments and specialized software.
The system is defined by several architectural characteristics:
- A complete knowledge library contained within a single package
- Standardized file structures that function across environments
- Browser-based access using local files rather than remote servers
- No requirement for installation, authentication, or connectivity
 This design ensures that the system is not tied to a specific operating system, device type, or software ecosystem. It operates within the lowest common denominator of digital systems—a web browser and a file system.
This design ensures that the system is not tied to a specific operating system, device type, or software ecosystem. It operates within the lowest common denominator of digital systems—a web browser and a file system.
Unlike traditional platforms, which require continuous operation of external infrastructure, this model shifts control entirely to the user. The system exists wherever it is stored, and its availability is determined solely by the presence of the files and a functioning device.
This approach reduces complexity while increasing control. It does not attempt to eliminate dependency entirely, but it minimizes it to the simplest and most reliable components available.
5.2 Access Model: Independence from External Systems
The defining feature of Prepper Offline™ is its access model. Unlike cloud-based systems or hardware-centric solutions, it does not rely on external validation, network connectivity, or centralized control.
Access is achieved through:
- Local file storage
- Standard browser rendering
- Direct navigation of structured content
This creates a system where access is immediate and predictable. There are no external calls, no authentication layers, and no dependency on real-time system availability.
In practical terms, this means that:
- If the files exist, the system is accessible
- If the device functions, the content can be used
- If the browser operates, the interface is available
This simplicity is intentional. It reduces the number of conditions required for the system to function, which in turn reduces the number of ways it can fail.
Compared to digital wealth systems, this model removes several layers of dependency:
- No network consensus required
- No cryptographic validation required
- No external infrastructure required
While digital wealth systems depend on continuous network operation to validate ownership and execute transactions, Prepper Offline™ depends only on local execution. This shifts the system from a dynamic, network-dependent model to a static, self-contained one.
The result is a system that trades real-time capability for reliability and independence.
5.3 Redundancy Model: Infinite Replication vs Centralized Storage
One of the most significant strengths of Prepper Offline™ lies in its redundancy model. Instead of protecting a single instance, it allows for unlimited duplication. The system can be copied across multiple devices, storage media, and locations without degradation.
This creates a fundamentally different approach to resilience.
Rather than asking:
· “How do I protect this system from failure?”
The system asks:
· “How many copies exist, and where are they stored?”
This shift changes the nature of risk.
In centralized systems, redundancy often requires complex infrastructure. Backups must be managed, synchronized, and maintained. In contrast, a file-based system allows redundancy through simple replication.
The advantages of this approach include:
- No dependency on synchronization or coordination
- No requirement for centralized backup systems
- Ability to distribute copies geographically
- Resilience against localized failure
From a failure perspective, this eliminates the concept of a single critical instance. If one copy is lost, others remain. If one device fails, access can be restored from another.
This model closely parallels the concept of distributed resilience found in decentralized systems, but without requiring active coordination or consensus.
Compared to digital wealth storage:
- A single hardware wallet represents concentrated risk
- A single exchange account represents custodial dependency
- A replicated file-based system distributes risk across multiple instances
The key insight is that:
Replication reduces risk more effectively than protection.
5.4 Failure Analysis: Eliminating Single Points of Failure
Every system has failure points. The goal of a resilient architecture is not to eliminate failure entirely, but to ensure that no single failure results in total loss of access.
Prepper Offline™ achieves this by reducing and distributing failure points across multiple layers.
Primary failure considerations include:
- Device failure
- Storage media corruption
- File damage or deletion
- User error
However, none of these represent total system failure unless they affect all copies simultaneously.
This creates a layered resilience model:
- Failure of one device → access continues through another
- Loss of one storage medium → backups remain available
- Corruption of one file set → other copies remain intact
The only true failure condition occurs when all instances are lost or inaccessible. This is significantly less likely than failure in systems that rely on a single point of access.
In contrast, other architectures exhibit more concentrated risk:
- Hardware-based systems fail completely if the device fails
- Online systems fail completely if access is lost
- Fragmented systems fail operationally when organization breaks down
Prepper Offline™ reduces these risks by separating knowledge from any single dependency.
This aligns with a core preparedness principle:
Systems should degrade gradually—not fail completely.
5.5 Alignment with Digital Wealth Principles
The architecture of Prepper Offline™ directly addresses many of the vulnerabilities identified in digital wealth systems. While the contexts differ—financial assets versus knowledge—the underlying principles are the same.
Digital wealth systems are defined by conditional access. Ownership depends on:
- Keys
- Networks
- Software compatibility
- Infrastructure availability
If any of these conditions fail, access is compromised.
Prepper Offline™ applies a different model. It reduces conditional access by removing as many dependencies as possible. Instead of relying on dynamic systems, it relies on static availability.
This creates a direct contrast:
Digital wealth systems:
- Depend on continuous operation
- Require validation and interaction
- Introduce multiple dependency layers
Prepper Offline™:
- Exists independently once created
- Requires no validation beyond file access
- Minimizes dependency layers
This does not mean the system is without risk. It still depends on:
- Physical storage
- Functional devices
- User management
However, these dependencies are simpler, more transparent, and easier to manage.
From a preparedness perspective, this leads to a clear interpretation:
- Digital wealth represents conditional control
- Prepper Offline™ represents conditional access with reduced dependency
The difference is not absolute independence, but reduced fragility.
5.6 Strategic Role in a Resilient Knowledge System
Prepper Offline™ is not intended to replace all other knowledge systems. Instead, it serves as a foundational layer within a broader strategy.
Its role is defined by:
- Providing reliable access under degraded conditions
- Serving as a primary offline reference system
- Supporting redundancy across multiple storage environments
- Reducing reliance on external infrastructure
When integrated with other systems, it forms part of a layered approach:
- Online systems provide scale and updates
- Physical systems provide durability
- Distributed digital systems provide accessibility and replication
This layered model mirrors best practices in financial preparedness, where no single asset class is relied upon exclusively.
The key advantage of Prepper Offline™ is that it provides a balance between:
- Accessibility
- Replicability
- Simplicity
- Control
It does not attempt to solve every problem. Instead, it addresses the most critical one:
Ensuring that knowledge remains accessible when other systems fail.
5.7 In Summary
Prepper Offline™ represents a distributed, file-based architecture designed to minimize dependency and maximize resilience.
Its key characteristics include:
- Self-contained structure with no external dependencies
- Browser-based access using standard tools
- Infinite replication for redundancy
- Elimination of single points of failure
- Reduced complexity compared to centralized systems
From a systems perspective, it achieves resilience not through protection, but through distribution and simplicity.
The core insight is:
A system that can be copied, distributed, and accessed independently is inherently more resilient than one that must be protected as a single instance.
Because in the end:
The strength of a system is not defined by how well it resists failure—but by how well it survives it.
6 PDF Collections — Fragmented Digital Architecture
6.1 System Design: Independent Files Without Unified Structure
 PDF collections represent one of the most common approaches to offline knowledge storage. They are easy to build, widely supported, and highly flexible. Users can gather documents from multiple sources over time and store them locally without requiring specialized systems.
PDF collections represent one of the most common approaches to offline knowledge storage. They are easy to build, widely supported, and highly flexible. Users can gather documents from multiple sources over time and store them locally without requiring specialized systems.
At a basic level, this approach appears effective. Each document exists independently, and access is not tied to an internet connection. However, this simplicity hides a deeper architectural limitation: the absence of a unified system.
 Unlike structured offline libraries, PDF collections are not designed as a cohesive whole. Instead, they are an accumulation of individual files, each with its own format, structure, and organization. There is no inherent relationship between documents beyond how the user chooses to organize them.
Unlike structured offline libraries, PDF collections are not designed as a cohesive whole. Instead, they are an accumulation of individual files, each with its own format, structure, and organization. There is no inherent relationship between documents beyond how the user chooses to organize them.
This architecture is defined by:
- Independent files with no shared framework
- Manual folder-based organization
- No built-in navigation or indexing system
- Reliance on external tools for access and search
While this allows for flexibility, it also creates fragmentation. As collections grow, the lack of structure becomes increasingly significant. Information is not lost—but it becomes harder to locate, interpret, and use efficiently.
From a systems perspective, this is not a unified knowledge system. It is a storage method.
6.2 Access Model: Tool-Dependent and User-Driven Retrieval
Access within a PDF collection depends heavily on the tools used to open and navigate the files. Unlike browser-based systems or structured libraries, there is no consistent interface across documents.
Users rely on:
- PDF readers or document viewers
- File explorers or operating system navigation
- Manual search within individual files
This introduces variability in access. Different devices may use different software, and different software may interpret documents differently. Features such as search, bookmarking, and rendering are not guaranteed to behave consistently.
In practical terms, this means:
- Access speed depends on user familiarity
- Navigation depends on file naming and organization
- Searching across documents is limited or inefficient
The system places a significant burden on the user. Instead of interacting with a unified interface, the user must manage multiple tools and workflows to retrieve information.
This becomes a critical limitation in time-sensitive scenarios. When information must be accessed quickly, the lack of structure can delay retrieval.
Compared to more integrated systems:
- There is no centralized index
- There is no cross-document navigation
- There is no standardized user experience
The system functions, but it requires active effort to use effectively.
6.3 Redundancy Model: Replicable but Disorganized
PDF collections benefit from one key advantage: they are easy to copy. Files can be duplicated across multiple devices, storage media, and locations with minimal effort. This provides a level of redundancy that reduces the risk of complete data loss.
However, this redundancy is often unstructured.
Copies may exist in multiple places, but without consistent organization, version control, or indexing. Over time, this can lead to:
- Duplicate files with inconsistent naming
- Outdated versions mixed with newer ones
- Missing or incomplete collections across backups
The system allows replication, but does not manage it.
This creates a situation where redundancy exists, but reliability is uncertain. A backup may contain the files, but not in a usable or organized form.
From a resilience perspective, this introduces a different type of risk:
- The system survives, but usability degrades
Unlike structured systems that maintain consistency across copies, PDF collections rely on manual discipline. The effectiveness of redundancy depends entirely on how well the user maintains the collection.
This parallels certain digital wealth scenarios, where assets may be backed up but poorly managed, leading to confusion or loss of access.
The key distinction is:
Replication without structure does not guarantee accessibility.
6.4 Failure Analysis: Usability Degradation Rather Than Total Loss
PDF collections rarely fail in a catastrophic way. Files are durable, and as long as storage media remains intact, the data persists. However, failure in this model occurs differently.
Instead of total system loss, the primary failure mode is usability degradation.
Common failure scenarios include:
- Inability to locate specific information quickly
- Loss of organizational structure
- Corrupt or incompatible files
- Missing dependencies (fonts, formatting, or embedded content)
In these cases, the information still exists, but accessing it becomes difficult or inefficient.
This is a critical distinction.
In high-stress situations, the difference between accessible and inaccessible information is not whether the data exists—it is whether it can be retrieved quickly and reliably.
PDF collections are particularly vulnerable to:
- Poor file naming conventions
- Deep or inconsistent folder structures
- Lack of indexing or categorization
As collections grow, these issues compound. What begins as a manageable system can become unwieldy over time.
Compared to other architectures:
- Online systems fail abruptly when access is lost
- Hardware systems fail when the device fails
- PDF collections fail gradually through complexity and disorganization
This gradual failure can be more difficult to detect. The system appears functional until it is needed under pressure.
6.5 Comparison to Digital Wealth: Management Complexity and Access Risk
The structure of PDF collections mirrors certain aspects of digital wealth systems, particularly in how complexity affects access.
In digital wealth, managing multiple wallets, keys, and storage methods introduces operational risk. The assets may be secure, but accessing them requires coordination and precision.
Similarly, PDF collections introduce:
- Organizational complexity
- Dependency on user knowledge
- Risk of mismanagement over time
Both systems share a common characteristic:
The asset exists, but access depends on proper management.
In digital wealth:
- Losing track of keys results in loss of access
In PDF collections:
- Losing track of files results in loss of usability
This creates a parallel between financial and knowledge systems:
- Security without usability reduces value
- Complexity increases the likelihood of failure
The risk is not that the system is insecure. The risk is that it becomes impractical to use when needed.
This reinforces a key principle from digital wealth doctrine:
Access must be maintained, not assumed.
6.6 Strategic Role in a Knowledge System
Despite its limitations, the PDF collection model still plays an important role in a broader knowledge strategy. Its strength lies in flexibility and accessibility during normal conditions.
PDF collections are well suited for:
- Expanding knowledge libraries quickly
- Storing specialized or niche documents
- Serving as a supplementary resource
However, they are less effective as a primary system for critical information that must be accessed quickly and reliably.
To be effective, PDF collections require:
- Consistent organization
- Clear naming conventions
- Periodic maintenance and cleanup
- Integration with more structured systems
When used in combination with structured offline systems, PDF collections can provide depth and breadth of information without being relied upon for immediate access.
This layered approach reduces the weaknesses of each system while leveraging their strengths.
6.7 In Summary
PDF collections represent a flexible but fragmented approach to offline knowledge storage.
Their key characteristics include:
- Independent, unstructured files
- Tool-dependent access
- Replicable but inconsistently organized redundancy
- Gradual failure through usability degradation
From an architectural perspective, they prioritize flexibility over structure.
The core limitation is not the absence of information, but the difficulty of accessing it efficiently under real conditions.
The key insight is:
A system that stores knowledge is not the same as a system that delivers knowledge.
Because in the end:
Information that cannot be quickly found and used is functionally equivalent to information that is not available at all.
7 Physical Books — Analog Resilience Model
7.1 System Design: Fully Independent Physical Storage
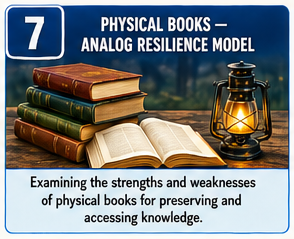 Physical books represent the most traditional form of knowledge storage, yet they remain one of the most resilient. Unlike digital systems, books do not rely on electronic infrastructure. They exist entirely within the physical world, requiring no power, no software, and no connectivity.
Physical books represent the most traditional form of knowledge storage, yet they remain one of the most resilient. Unlike digital systems, books do not rely on electronic infrastructure. They exist entirely within the physical world, requiring no power, no software, and no connectivity.
This independence defines their architecture.
A physical book is:
- A self-contained unit of information
- Accessible without tools or intermediaries
- Independent of technological systems
- Durable under stable environmental conditions
Once acquired, the knowledge within a book is immediately available. There are no layers of abstraction, no interpretation required by software, and no dependency on system compatibility.
 This simplicity is a significant advantage. It eliminates entire categories of failure that affect digital systems. There are no file formats to become obsolete, no devices to malfunction, and no systems to update.
This simplicity is a significant advantage. It eliminates entire categories of failure that affect digital systems. There are no file formats to become obsolete, no devices to malfunction, and no systems to update.
However, this independence comes with structural limitations. Each book exists as a single physical object. It cannot be duplicated instantly, distributed easily, or scaled without effort.
From an architectural perspective, physical books trade flexibility for independence. They remove technological dependency but introduce physical constraints.
7.2 Access Model: Direct Human Interaction Without Intermediaries
The access model for physical books is fundamentally different from digital systems. It is direct, immediate, and requires no intermediary.
Access is achieved through:
- Physical possession of the book
- Human ability to read and interpret content
- Manual navigation through pages and sections
There is no interface beyond the book itself. The user interacts directly with the information without relying on tools or systems to interpret or deliver it.
This creates a highly reliable access model. As long as the book is present and intact, the information is available. There are no delays, no loading times, and no system dependencies.
However, this model also introduces limitations:
- Searching is manual rather than automated
- Navigation depends on indexes or memory
- Retrieval speed is slower compared to digital systems
In time-sensitive situations, this can be a disadvantage. While the information is always available, locating specific details may take time and effort.
Compared to digital systems:
- There is no search function
- There is no dynamic indexing
- There is no cross-referencing beyond what is printed
The system is stable, but not optimized for speed or scale.
7.3 Redundancy Model: Physical Duplication and Distribution Limits
Redundancy in physical systems operates differently from digital systems. While digital files can be copied instantly, physical books must be reproduced individually.
This creates a more constrained redundancy model.
To create redundancy, one must:
- Acquire multiple copies
- Store them in different locations
- Protect them from environmental risks
This process requires time, effort, and resources. Unlike digital systems, there is no simple method for large-scale replication.
As a result, redundancy is often limited. Many users rely on a single copy of a book, which introduces a clear point of vulnerability.
The limitations include:
- Difficulty of mass duplication
- Storage space requirements
- Physical weight and transport constraints
- Cost associated with acquiring multiple copies
However, when redundancy is intentionally implemented, physical systems can be highly resilient. Multiple copies stored in different locations can provide strong protection against localized loss.
From a preparedness perspective, redundancy must be planned rather than assumed.
7.4 Failure Analysis: Physical Loss and Environmental Risk
Physical books do not fail in the same way digital systems do. They do not become inaccessible due to software issues or network failures. Instead, their failure modes are tied to the physical environment.
Primary failure risks include:
- Fire damage
- Water exposure
- Mold and decay
- Physical destruction or loss
These risks are often localized but can be severe. A single event can destroy an entire collection if it is stored in one location.
Unlike digital systems, physical books do not degrade gracefully. When damage occurs, it is often permanent.
However, physical systems are not subject to:
- Software corruption
- Format incompatibility
- Device failure
- Network disruption
This creates a different risk profile.
- Digital systems fail through dependency loss
- Physical systems fail through environmental impact
The key difference is that physical failures are often visible and predictable, while digital failures can be hidden and complex.
From a resilience standpoint, physical systems benefit from simplicity but require protection against environmental factors.
7.5 Comparison to Digital Wealth: Hard Assets vs System-Dependent Value
The role of physical books in knowledge systems closely parallels the role of hard assets in financial systems.
In digital wealth systems, value is abstract and system-dependent. It relies on networks, cryptography, and infrastructure. In contrast, physical assets such as gold or cash exist independently of these systems.
Physical books occupy a similar position in knowledge systems.
They are:
- Tangible
- Independent of digital infrastructure
- Accessible without system validation
- Not subject to technological failure
This makes them highly reliable under certain conditions.
However, like physical assets, they also have limitations:
- Lack of portability compared to digital systems
- Difficulty of scaling and distribution
- Reduced flexibility in use
The comparison highlights a key trade-off:
- Digital systems offer efficiency and scalability
- Physical systems offer independence and certainty
Neither is inherently superior. Each addresses different risks.
From a preparedness perspective, physical books provide a baseline level of resilience that does not depend on external systems. They act as a fallback when digital systems are unavailable.
7.6 Strategic Role in a Knowledge System
Physical books are best understood as a foundational layer within a broader knowledge strategy. They provide stability and independence, but are not sufficient on their own for comprehensive coverage.
Their ideal role includes:
- Serving as a backup to digital systems
- Providing critical knowledge in high-risk scenarios
- Supporting long-term durability of essential information
They are particularly valuable for:
- Core survival knowledge
- High-priority reference materials
- Information that must remain accessible under all conditions
However, they are less effective for:
- Large-scale information storage
- Rapid search and retrieval
- Frequent updates or dynamic content
When integrated with digital systems, physical books provide a layer of redundancy that protects against technological failure.
This layered approach reflects a broader preparedness principle:
No single system should be relied upon exclusively.
7.7 In Summary
Physical books represent an analog, independent approach to knowledge storage.
Their key characteristics include:
- Complete independence from digital infrastructure
- Direct, tool-free access
- Limited scalability and duplication
- Vulnerability to environmental damage
From an architectural perspective, they prioritize simplicity and independence over flexibility and efficiency.
The core strength of physical books lies in their reliability. They do not depend on systems that can fail unexpectedly. However, they require intentional management to mitigate physical risks.
The key insight is:
Independence reduces complexity, but introduces physical constraints.
Because in the end:
A system that cannot fail digitally must still be protected physically.
8 Online Websites — Cloud-Dependent Knowledge Systems
8.1 System Design: Centralized, Infrastructure-Dependent Architecture
 Online knowledge systems represent the dominant method of accessing information today. They provide scale, speed, and convenience that no offline system can fully match. However, this capability is built on a highly centralized and infrastructure-dependent architecture.
Online knowledge systems represent the dominant method of accessing information today. They provide scale, speed, and convenience that no offline system can fully match. However, this capability is built on a highly centralized and infrastructure-dependent architecture.
At their core, online systems are not owned by the user. They are hosted, managed, and controlled by external entities. The user interacts with the system, but does not control it.
A practical example of this model is Prepping Communities, which operates as a cloud-based knowledge platform. It provides a structured environment where users can access a full catalog of preparedness content through:
- Centralized content management
- Searchable postings and categorized knowledge
- Dynamic updates and continuous content expansion
- Integrated user interaction and discovery features
 This architecture is defined by:
This architecture is defined by:
- Centralized servers hosting content
- Continuous reliance on internet connectivity
- Platform-controlled access and permissions
- Dynamic content that is updated in real time
Unlike offline systems, where knowledge is stored locally, online systems separate the user from the information. The content exists elsewhere, and access depends on the ability to connect to that location.
This separation introduces multiple layers of dependency. The system does not fail gradually—it fails when access is interrupted.
From an architectural perspective, this model prioritizes:
- Scalability
- Real-time updates
- Centralized management
But these advantages come at the cost of independence.
8.2 Access Model: Conditional and Externally Controlled
The defining feature of online systems is that access is conditional. The user does not directly interact with stored knowledge. Instead, they request access through a series of systems that must all function correctly.
Access depends on:
- A functioning device
- Reliable power
- Stable internet connectivity
- Operational servers
- Valid access permissions
If any one of these conditions fails, access is interrupted.
This creates a layered access model where control is distributed across multiple entities and systems. The user may initiate the request, but does not control the outcome.
In practical terms, this means:
- Information is available only when systems are operational
- Access can be delayed, restricted, or removed
- The user cannot guarantee availability under all conditions
This contrasts sharply with offline systems, where access is determined by local conditions rather than external systems.
The convenience of online access often masks this dependency. Because systems function reliably under normal conditions, users assume that access is permanent. In reality, it is continuously dependent on infrastructure that is outside their control.
8.3 Redundancy Model: Centralized Control with Distributed Infrastructure
Online systems often appear resilient due to the scale of their infrastructure. Large platforms use distributed servers, data centers, and backup systems to ensure availability. This creates the impression of redundancy.
However, this redundancy is not user-controlled.
The system may be distributed at the infrastructure level, but from the user’s perspective, access remains centralized. The user interacts with a single platform, and their ability to access information depends on that platform’s continued operation.
This creates a key distinction:
- Infrastructure redundancy exists
- User-level redundancy does not
If a platform becomes unavailable—due to technical failure, policy decisions, or external disruption—the user cannot access the system, regardless of how robust the underlying infrastructure may be.
However, in the case of Prepping Communities, there is an important architectural extension. The entire body of online knowledge—including all postings, structure, and content—is designed to be exported and replicated into the Prepper Offline™ system.
This creates a hybrid model:
- Online system → discovery, search, and continuous updates
- Offline system → replication, control, and resilient access
This linkage between systems is significant. It allows the centralized platform to serve as a source of truth while enabling users to transition that knowledge into a distributed, user-controlled environment.
8.4 Failure Analysis: Total Access Loss Under Disruption
Online systems exhibit a distinct failure pattern. They function efficiently under normal conditions but fail completely when dependencies are disrupted.
Primary failure scenarios include:
- Loss of internet connectivity
- Power outages affecting local or remote systems
- Server outages or platform failures
- Access restrictions or account limitations
In each case, the result is the same:
Access is lost entirely.
Unlike other systems that degrade gradually, online systems do not provide partial functionality when disrupted. There is no fallback mode, no limited access, and no local backup within the system itself.
This creates a binary condition:
- The system is available
- The system is unavailable
There is no intermediate state.
However, the existence of Prepper Offline™ fundamentally alters this failure model for users who adopt a hybrid approach. Because the entire online library can be replicated into an offline format, the loss of online access does not necessarily result in loss of information.
Instead, the failure shifts from:
- Total loss of access
to:
- Loss of centralized features (search, updates, interaction)
while maintaining:
- Continued access to core knowledge offline
This represents a significant reduction in overall system risk.
8.5 Comparison to Digital Wealth: Custodial and Exchange-Based Systems
The structure of online knowledge systems closely mirrors custodial digital wealth systems, such as cryptocurrency exchanges.
In both cases:
- The user interacts with a centralized platform
- Access is mediated by external systems
- Control is limited to what the platform allows
In digital wealth systems:
- Assets stored on exchanges are accessible only through the platform
- Users rely on the platform’s stability and policies
- Access can be restricted or lost without direct user control
Similarly, in online knowledge systems:
- Information is accessed through a platform
- Availability depends on system operation
- Users cannot guarantee access independently
This creates a parallel between the two domains:
- Custodial wealth systems → Conditional financial access
- Online knowledge systems → Conditional information access
However, the integration of Prepper Offline™ introduces a structural advantage not commonly found in digital wealth systems.
Users are able to:
- Experience the full system online
- Evaluate its content and usability
- Replicate that content into an offline environment
- Transition from conditional access to controlled access
This effectively allows users to “test” the system in a centralized environment before migrating to a distributed one.
This model reduces uncertainty and increases adoption while maintaining resilience.
8.6 Strategic Role in a Knowledge System
Despite their limitations, online systems play an essential role in a comprehensive knowledge strategy. Their strength lies in scale, accessibility, and the ability to provide up-to-date information.
Online systems are well suited for:
- Research and information discovery
- Accessing current and evolving knowledge
- Expanding knowledge libraries
- Providing a structured and searchable interface
In the case of Prepping Communities, the platform serves as:
- A centralized knowledge hub
- A discovery and learning environment
- A fully searchable catalog of preparedness content
However, it is not intended to be the final layer of control.
Its strategic role is to act as:
- The primary source of knowledge acquisition
- The interface for exploration and organization
- The upstream system that feeds into offline resilience
When paired with Prepper Offline™, the system becomes:
- Online → dynamic, scalable, discoverable
- Offline → stable, replicable, resilient
This dual-layer architecture combines the strengths of both models while reducing their individual weaknesses.
8.7 In Summary
Online websites represent a centralized, infrastructure-dependent approach to knowledge systems.
Their key characteristics include:
- Centralized control of content and access
- Dependence on power, connectivity, and server infrastructure
- Conditional access based on system availability
- Complete loss of access under disruption
However, when integrated with Prepper Offline™, this model evolves into a hybrid architecture that significantly reduces risk.
This hybrid system provides:
- Full online access for discovery and usability
- Complete offline replication for resilience and control
From an architectural perspective, this creates a transition from:
- Conditional access
to:
- Controlled access with reduced dependency
The key insight is:
A centralized system becomes significantly more resilient when its content can be fully replicated into a distributed environment.
Because in the end:
The most powerful system is not the one you can access online—but the one you can still access when you cannot.
9 Hardware-Centric Architecture
9.1 System Design: Server-in-a-Box Architecture
 Hardware centric architecture solutions like Prepper Disk™ represent a hardware-centric approach to offline knowledge systems. Unlike file-based models that distribute content across multiple environments, this model consolidates both storage and access into a single physical device.
Hardware centric architecture solutions like Prepper Disk™ represent a hardware-centric approach to offline knowledge systems. Unlike file-based models that distribute content across multiple environments, this model consolidates both storage and access into a single physical device.
At its core, Prepper Disk™ functions as a “server-in-a-box.” It contains the knowledge library, the software required to access it, and the interface through which users interact with the content. This creates a controlled and self-contained environment designed to operate without internet connectivity.
Authors Note
 Let me start by saying that we genuinely like Prepper Disk™ and believe it serves a unique role in offline storage and access to large amounts of information. We purchased the device ourselves and were pleased overall with what we received. While it is relatively expensive (we paid over $300), it comes as a pre-configured Raspberry Pi system tailored for offline use, loaded with a substantial amount of public domain content along with some proprietary material.
Let me start by saying that we genuinely like Prepper Disk™ and believe it serves a unique role in offline storage and access to large amounts of information. We purchased the device ourselves and were pleased overall with what we received. While it is relatively expensive (we paid over $300), it comes as a pre-configured Raspberry Pi system tailored for offline use, loaded with a substantial amount of public domain content along with some proprietary material.
We appreciated the 500GB of storage capacity and the flexibility to add our own content if needed. That said, we did encounter a few areas that felt awkward or less intuitive—some of which are discussed elsewhere in this document from an architectural perspective, and others based on our direct experience:
- Prepper Disk seems to have been built to provide an offline solution based on internet in a box. That is, it’s primary purpose is an internet server that people connect their devices to access the content. This architecture has several important constraints;
- it represents a single point of failure meaning if the hardware experiences any problem, all users are down and cannot access the offline content
- while the server hardware allows multiple people to connect simultaneously, every user requires their own device to connect to the server. while this is not necessarily a problem, it does mean using Prepper Disk requires a minimum of two devices to access the content (when access to any device may be at a premium, or missing all together).
- By default, using the system requires connecting another device through Wi-Fi. While that’s not inherently an issue, it became inconvenient when we wanted to maintain our normal internet connection while also accessing Prepper Disk™. Resolving this required navigating the admin settings, which took some time to figure out.
- The device itself is well-configured, but for users already familiar with Raspberry Pi systems, there isn’t anything particularly unique about the underlying setup. There is very little ‘new’, and not public domain content, provided by the manufacturers. The main value comes from the fact that it is packaged and ready to use, which is ideal for non-technical users. In our case, we had already built similar hardware-based offline storage systems using many of the same content sources.
- The interface is simple and brings together a large amount of content and tools in one place. However, we found that search functionality was limited. In most cases, search was confined within individual documents (such as encyclopedias) rather than across the entire content library. In a time-sensitive situation, the ability to search across all available content quickly is critical.
- From a usability standpoint, we found the system somewhat challenging for non-technical users. That may be intentional, as many preppers interested in this type of device tend to have a higher level of technical comfort.
Although Prepper Disk has some architectural limitations, as discussed throughout this document, we still see value in it as part of a broader preparedness toolkit. As mentioned earlier, no single solution should be relied upon exclusively. A resilient approach includes a mix of offline resources—such as physical books, Prepper Disk™, PDF collections, and Prepper Offline™—each offering its own strengths and trade-offs.
The architecture is defined by:
- A dedicated hardware device acting as the central system
- Locally hosted content stored on internal storage
- Integrated software environment for navigation and access
- Controlled access through a local network or direct connection
This design attempts to combine the advantages of online systems—structured content and user-friendly interfaces—with the independence of offline operation.
However, this consolidation introduces a critical characteristic:
All system functionality is concentrated within a single physical unit.
Unlike distributed systems, where knowledge exists across multiple copies, the Prepper Disk™ model centralizes both data and access into one device. This simplifies deployment but increases dependency on that device.
From an architectural perspective, this is a high-control, high-concentration system.
9.2 Access Model: Localized but Device-Dependent
The access model for Prepper Disk™ is local rather than remote, which removes reliance on external networks. Users connect directly to the device, either through a local network or a direct interface, to access the stored content.
Access depends on:
- A functioning hardware device
- Power availability
- The device’s internal software environment
- Network connectivity within the local system (if required)
This creates a system that is independent of the internet but still dependent on internal infrastructure.
In practical terms:
- If the device is operational, access is available
- If the device fails, access is lost entirely
- If the interface becomes unusable, content cannot be retrieved
This model reduces external dependency but does not eliminate dependency—it shifts it inward.
Compared to other systems:
- Online systems depend on external infrastructure
- File-based systems depend on distributed local storage
- Hardware systems depend on a single internal device
The advantage is simplicity of access within a controlled environment. The limitation is that access is tied directly to the health of a single system.
9.3 Redundancy Model: Limited by Physical Replication
Redundancy in a hardware-centric system is fundamentally constrained by the physical nature of the device. Unlike file-based systems that allow unlimited duplication, Prepper Disk™ requires full device replication to achieve redundancy.
To create redundancy, users must:
- Maintain multiple devices
- Synchronize content across those devices
- Store devices in separate locations
This introduces several limitations:
- Higher cost compared to file duplication
- Increased complexity in maintaining multiple systems
- Greater logistical effort to distribute backups
In most cases, users operate with a single device. This creates an implicit assumption that the device will remain functional, which introduces risk.
Even when backups exist, they are often not maintained at the same level of readiness. A secondary device may not be updated, powered, or accessible when needed.
This creates a redundancy gap:
- Redundancy exists in theory
- Redundancy may not exist in practice
From a resilience perspective, this model does not naturally support distributed redundancy. It requires intentional effort and resources to achieve what file-based systems accomplish inherently.
9.4 Failure Analysis: Single Point of Failure and System Collapse
The most significant risk in a hardware-centric architecture is the presence of a single point of failure. Because all functionality is concentrated within one device, failure of that device results in total system failure.
Primary failure scenarios include:
- Hardware malfunction or degradation
- Power failure without backup systems
- Storage corruption or drive failure
- Software malfunction within the device
In each case, the result is the same:
The system becomes inaccessible.
Unlike distributed systems, there is no fallback within the architecture itself. The system does not degrade gradually—it fails completely when the device fails.
This creates a high-impact failure model:
- One failure event → complete loss of access
Even when backups exist, recovery requires:
- Access to a secondary device
- Restoration of the system environment
- Verification of data integrity
This introduces delay and uncertainty, particularly in time-sensitive situations.
Compared to other architectures:
- Distributed systems degrade gradually through partial loss
- Fragmented systems degrade through usability issues
- Hardware systems fail abruptly and completely
This abrupt failure profile is a critical consideration in preparedness planning.
9.5 Comparison to Digital Wealth: Hardware Wallet Concentration Risk
The architecture of Prepper Disk™ closely parallels the use of hardware wallets in digital wealth systems.
In both cases:
- Control is centralized within a physical device
- Security and access are tied to that device
- Failure of the device introduces significant risk
Hardware wallets provide strong isolation from external threats, but they concentrate risk into a single point. If the device is lost, damaged, or inaccessible, the user must rely on backup mechanisms to recover access.
Similarly, Prepper Disk™ provides:
- Controlled, isolated access to knowledge
- Independence from external systems
- A structured and contained environment
However, it also introduces:
- Dependence on a single hardware unit
- Risk of total access loss if the device fails
- Requirement for external backup strategies
This creates a trade-off:
- Increased control and simplicity
- Increased concentration of risk
In digital wealth doctrine, this is understood as concentration risk. The same principle applies here.
The system is secure and controlled, but only as long as the device remains functional.
9.6 Strategic Role in a Knowledge System
Prepper Disk™ occupies a specific role within a broader knowledge strategy. It is best suited for users who prioritize a controlled, structured environment with minimal external dependency.
Its strengths include:
- A unified interface for accessing content
- Local hosting without reliance on internet connectivity
- Controlled environment for managing knowledge
However, it is not inherently resilient without additional planning.
To function effectively, it requires:
- Backup devices or alternative access methods
- Power redundancy (battery or generator support)
- Regular maintenance and updates
When integrated into a layered system, Prepper Disk™ can serve as:
- A primary access point for structured knowledge
- A local server for controlled environments
- A bridge between online systems and offline access
However, it should not be relied upon as the sole repository of critical knowledge.
Its role is strongest when combined with distributed systems that provide redundancy beyond the device itself.
9.7 In Summary
Prepper Disk™ represents a hardware-centric approach to offline knowledge systems, combining structured access with local independence.
Its key characteristics include:
- Centralized control within a single device
- Local access without internet dependency
- Limited redundancy due to physical constraints
- High-impact failure due to single point of failure
From an architectural perspective, it prioritizes control and simplicity within a contained environment.
The core limitation is not access under normal conditions, but resilience under failure.
The key insight is:
A system that concentrates functionality into a single device concentrates risk into that device.
Because in the end:
The strength of a system is not defined by how well it performs when it works—but by what happens when it stops working.
10 Dependency Mapping Across All Systems
10.1 Understanding Dependency as the Root of Fragility
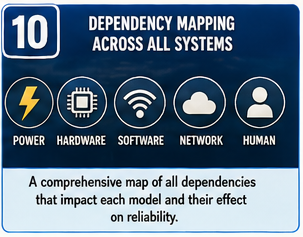 Every knowledge system, regardless of how it is designed, depends on something. These dependencies are often invisible during normal operation, which creates the illusion that systems are more resilient than they actually are.
Every knowledge system, regardless of how it is designed, depends on something. These dependencies are often invisible during normal operation, which creates the illusion that systems are more resilient than they actually are.
Dependency is the foundation of fragility.
A system does not fail randomly. It fails when one or more of its required conditions are no longer met. The more conditions a system depends on, the greater the number of ways it can fail.
In modern knowledge systems, dependencies are layered. They are not limited to a single component, but exist across multiple dimensions:
- Physical infrastructure
- Technical systems
- Environmental conditions
- Human interaction
These dependencies interact with each other. A failure in one layer can cascade into others, amplifying the overall impact.
Understanding these dependencies is essential for evaluating resilience. Without this understanding, systems are judged based on how they perform under ideal conditions rather than how they behave under stress.
The goal of dependency mapping is not to eliminate dependency entirely—this is not possible. Instead, it is to identify where dependencies exist, how critical they are, and how they can be reduced or managed.
This approach shifts the focus from system capability to system survivability.
10.2 Power Dependency
Power is one of the most fundamental dependencies in any system. Without it, most digital systems become immediately unusable.
Different knowledge systems rely on power in different ways.
- Online systems require continuous power across multiple locations
- Hardware-based systems require power to operate the device
- File-based systems require power only at the point of access
- Physical books require no power at all
This creates varying levels of vulnerability.
Systems that depend on continuous power are exposed to a broader range of failure scenarios. A disruption in power—whether local or remote—can immediately impact access.
In contrast, systems that require power only intermittently are more resilient. They can function as long as power is available at the moment of use, rather than continuously.
Physical systems eliminate this dependency entirely. However, they introduce other constraints that must be considered.
The key distinction is:
- Continuous power dependency → higher risk
- Intermittent power dependency → moderate risk
- No power dependency → minimal risk
From a preparedness perspective, reducing reliance on continuous power is a critical step in improving resilience.
10.3 Hardware Dependency
Hardware forms the physical foundation of digital knowledge systems. Without functioning devices, digital information cannot be accessed, regardless of how well it is stored.
The degree of hardware dependency varies significantly between systems.
- Prepper Disk™ concentrates dependency into a single device
- PDF collections rely on any compatible device but require one to function
- Prepper Offline™ allows access across multiple devices and storage media
- Online systems depend on both local and remote hardware infrastructure
This creates different risk profiles.
Systems that concentrate hardware dependency into a single device are more vulnerable to catastrophic failure. If that device fails, access is lost.
Systems that distribute hardware dependency across multiple devices reduce this risk. If one device fails, another can be used to access the same information.
Online systems introduce an additional layer of dependency. They rely not only on the user’s device, but also on remote servers and infrastructure. This multiplies the number of potential failure points.
The key insight is:
- Concentrated hardware dependency → single point of failure
- Distributed hardware dependency → reduced risk
- Multi-layer hardware dependency → increased complexity and fragility
Resilient systems minimize reliance on any single piece of hardware.
10.4 Software Dependency
Software determines how digital information is interpreted and accessed. Without compatible software, data may exist but remain unusable.
Different systems introduce different levels of software dependency.
- PDF collections depend on document readers and file compatibility
- Prepper Disk™ depends on its internal software environment
- Online systems depend on platform software and interfaces
- Prepper Offline™ relies on standard browser functionality
Software dependency introduces several risks:
- Compatibility issues across devices
- Obsolescence of formats or applications
- Corruption or malfunction of software environments
Systems that rely on proprietary or specialized software are particularly vulnerable. If the required software is unavailable or incompatible, access is lost.
In contrast, systems that use widely supported, standardized tools are more resilient. A browser-based system, for example, benefits from broad compatibility and long-term support.
The distinction can be summarized as:
- Specialized software dependency → higher risk
- Standardized software dependency → lower risk
Reducing software complexity improves long-term accessibility.
10.5 Network Dependency
Network dependency is one of the most significant factors distinguishing online and offline systems.
- Online systems require continuous network connectivity
- Prepper Disk™ may require local network access
- File-based systems operate without network dependency
- Physical systems operate entirely outside network environments
Network dependency introduces a critical vulnerability:
If the network fails, access fails.
Unlike other dependencies, network failure often results in immediate and complete loss of access. There is no partial functionality or degraded mode.
This creates a binary condition for network-dependent systems:
- Connected → functional
- Disconnected → non-functional
In contrast, systems without network dependency maintain consistent access regardless of external conditions.
From a resilience perspective:
- High network dependency → high risk
- Local network dependency → moderate risk
- No network dependency → minimal risk
Eliminating network dependency is one of the most effective ways to improve system reliability.
10.6 Human Dependency
Human dependency is often overlooked but plays a critical role in system usability. A system that cannot be easily understood or used under stress is effectively inaccessible.
Human dependency includes:
- Knowledge of how to operate the system
- Ability to navigate and retrieve information
- Familiarity with tools and interfaces
- Cognitive load required to use the system
Different systems place different demands on the user.
- PDF collections require manual organization and navigation
- Prepper Disk™ requires understanding of device operation
- Online systems require familiarity with interfaces and search
- Prepper Offline™ reduces complexity through structured access
- Physical books require manual search and interpretation
In high-stress situations, complexity becomes a failure point. Systems that require significant effort to use are more likely to fail when they are needed most.
The key consideration is:
- High cognitive load → increased risk of failure
- Low cognitive load → improved reliability
Resilient systems are not only technically robust—they are also easy to use under real conditions.
10.7 Comparative Dependency Profile
When all dependency layers are considered together, each system reveals a distinct profile.
- Online systems exhibit high dependency across all layers
- Hardware systems reduce network dependency but concentrate hardware risk
- PDF collections reduce network dependency but increase human and organizational dependency
- Physical books eliminate digital dependency but introduce physical limitations
- Prepper Offline™ reduces dependency across multiple layers through simplicity and distribution
This comparative view highlights a central principle:
No system eliminates dependency.
Each system shifts dependency to different layers.
Understanding where those dependencies exist allows for better system design and more effective risk management.
10.8 In Summary
Dependency mapping reveals the underlying structure of knowledge systems and the sources of their fragility.
Key insights include:
- Systems fail when their dependencies are not met
- More dependencies increase the likelihood of failure
- Concentrated dependencies create single points of failure
- Distributed dependencies reduce risk but require structure
From a preparedness perspective, the goal is not to eliminate dependency entirely, but to:
- Reduce the number of critical dependencies
- Distribute remaining dependencies across multiple layers
- Ensure that failure in one area does not result in total system loss
The key insight is:
Resilience is not determined by what a system can do—it is determined by what it does not depend on.
Because in the end:
The fewer conditions required for access, the more reliable that access becomes.
11 Failure Scenarios (Applied Analysis)
11.1 Why Scenario-Based Analysis Matters
 Understanding system architecture provides a theoretical framework, but it does not fully capture how systems behave under real-world conditions. Systems are rarely stressed under ideal circumstances. Instead, they are tested during moments of disruption—when multiple dependencies fail simultaneously or in rapid succession.
Understanding system architecture provides a theoretical framework, but it does not fully capture how systems behave under real-world conditions. Systems are rarely stressed under ideal circumstances. Instead, they are tested during moments of disruption—when multiple dependencies fail simultaneously or in rapid succession.
Scenario-based analysis shifts the focus from design to performance. It evaluates not what a system is intended to do, but what it actually does when conditions degrade. This distinction is critical because many systems that appear robust in theory reveal hidden weaknesses when exposed to stress.
In preparedness planning, assumptions about reliability must be replaced with tested outcomes. By applying specific failure scenarios, it becomes possible to observe how systems behave, where they fail, and whether they can continue to provide value under adverse conditions.
Failure rarely occurs in isolation. It often presents as overlapping disruptions:
- Power loss affecting both local and remote systems
- Hardware failure occurring alongside limited recovery options
- Network disruption coinciding with increased demand for information
Scenario-based analysis allows for a more realistic evaluation of system resilience by examining how these conditions interact.
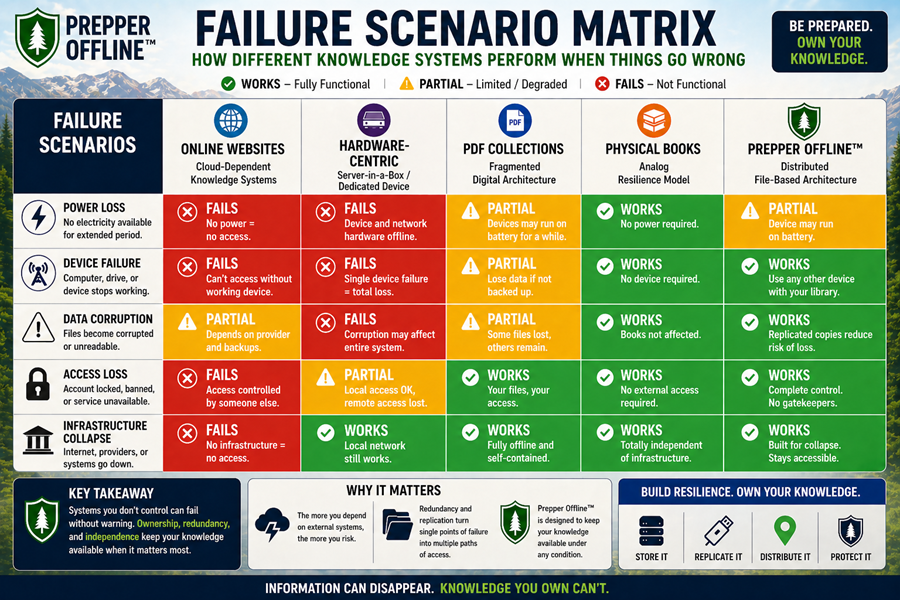
11.2 Scenario 1: Power Loss
Power loss is one of the most immediate and universally disruptive failure scenarios. It affects not only individual devices but also the infrastructure that supports digital systems. Unlike other forms of failure, power loss does not degrade performance—it stops it.
When power is removed, systems that depend on continuous operation fail instantly. There is no transition period, no partial functionality, and no recovery without external intervention. This makes power dependency one of the most critical factors in evaluating system resilience.
Under power loss conditions:
- Online systems become inaccessible immediately
- Prepper Disk™ becomes unusable unless backup power exists
- PDF collections cannot be accessed without a powered device
- Prepper Offline™ remains accessible only when power is restored locally
- Physical books remain fully accessible
This scenario highlights a fundamental distinction between systems that require continuous power and those that do not. Systems that operate independently of power provide uninterrupted access, while others depend on restoration.
The key insight is that power dependency defines baseline reliability. Systems that require constant power are inherently more vulnerable to disruption.
11.3 Scenario 2: Device Failure
Device failure represents a localized but high-impact event. Unlike power loss, which affects entire systems, device failure isolates the problem to a single point. However, depending on the system architecture, this single failure can have widespread consequences.
The impact of device failure is determined by how knowledge is distributed. If all information is tied to one device, that device becomes a critical point of failure. If information exists across multiple devices, the system can continue to function despite the loss of one component.
Under device failure conditions:
- Prepper Disk™ loses all functionality if the device fails
- PDF collections become inaccessible if stored on a single device
- Online systems remain accessible through alternate devices (if network is available)
- Prepper Offline™ remains accessible if replicated across multiple devices
- Physical books remain unaffected
This scenario illustrates the importance of distribution. Systems that allow access from multiple devices reduce the impact of localized failure.
The key distinction is not whether a device can fail—it is whether the system can continue without it.
11.4 Scenario 3: Data Corruption
Data corruption is a less visible but equally significant failure scenario. Unlike hardware failure, where the problem is immediately apparent, corrupted data may not be detected until access is attempted.
This creates a unique challenge. A system may appear intact, but critical information may be unusable when needed. The failure is not in the storage of data, but in its integrity.
Data corruption can occur due to:
- Storage degradation
- File system errors
- Software conflicts
- Improper handling or transfer
Under data corruption conditions:
- Prepper Disk™ may lose access to corrupted files or the entire system
- PDF collections may lose individual documents
- Online systems are generally unaffected due to centralized backups
- Prepper Offline™ may lose a single instance but retains access through other copies
- Physical books may be damaged but not digitally corrupted
This scenario highlights the importance of redundancy. Systems that maintain multiple independent copies can recover from corruption without external intervention.
The key insight is that data integrity cannot be assumed. It must be protected through replication and validation.
11.5 Scenario 4: Access Loss (Permissions, Platform, or Availability)
Access loss represents a failure condition where the information still exists, but the ability to retrieve it is removed. This is one of the most overlooked risks in modern systems, particularly those that rely on external platforms.
In many cases, users assume that access is permanent because the system is available under normal conditions. However, access can be restricted, altered, or removed entirely without affecting the underlying data.
Access loss can occur due to:
- Platform outages
- Account restrictions or changes
- Policy or permission changes
- System-level failures
Under access loss conditions:
- Online systems become completely inaccessible
- Prepper Disk™ remains accessible if the device is operational
- PDF collections remain accessible locally
- Prepper Offline™ remains fully accessible
- Physical books remain unaffected
This scenario reinforces the distinction between access and ownership. Systems that rely on external control cannot guarantee access under all conditions.
The key insight is that access controlled by external systems is inherently conditional.
11.6 Scenario 5: Infrastructure Collapse
Infrastructure collapse represents a large-scale failure scenario where multiple systems fail simultaneously. This may include prolonged power outages, widespread network disruption, or breakdown of centralized services.
Unlike isolated failures, infrastructure collapse affects multiple layers of dependency at once. Systems that rely on interconnected infrastructure are particularly vulnerable, as failure in one area can cascade into others.
Under infrastructure collapse conditions:
- Online systems become completely unusable
- Prepper Disk™ functions only if power and device integrity are maintained
- PDF collections function only with available devices and power
- Prepper Offline™ functions under the same conditions but benefits from distributed storage
- Physical books remain fully functional
This scenario highlights the importance of independence. Systems that operate outside of infrastructure dependencies maintain functionality, while others fail entirely.
However, even offline digital systems require minimal infrastructure—primarily power and functional devices. This places them in an intermediate position between fully dependent and fully independent systems.
The key insight is that resilience increases as dependency on external infrastructure decreases.
11.7 Comparative Scenario Behavior
When multiple scenarios are analyzed together, patterns begin to emerge. Each system responds differently to stress, revealing its underlying strengths and weaknesses.
Some systems perform well under normal conditions but fail abruptly when disrupted. Others degrade gradually, maintaining partial functionality even as conditions worsen. A few remain stable across most scenarios but are limited in other ways.
Across all scenarios:
- Online systems perform best under normal conditions but fail completely under disruption
- Hardware systems function reliably until device failure, then fail completely
- PDF collections degrade through complexity and usability challenges
- Physical books remain consistently accessible but limited in scale
- Prepper Offline™ maintains access across most scenarios due to distribution and simplicity
This comparison highlights an important principle:
Resilience is defined by continuity, not performance.
The ability to maintain access, even at reduced capacity, is more valuable than peak performance under ideal conditions.
11.8 In Summary
Failure scenarios provide a practical lens through which to evaluate knowledge systems. They reveal how systems behave under stress, where dependencies exist, and how access is affected when those dependencies fail.
Key insights include:
- Systems dependent on continuous operation are most vulnerable
- Systems with single points of failure exhibit high-impact risk
- Systems that distribute data and access are more resilient
- Systems that reduce dependency provide greater continuity
From a preparedness perspective, the objective is not to eliminate failure, but to design systems that continue to function despite it.
The key insight is:
A resilient system is defined not by its ability to avoid failure, but by its ability to maintain access when failure occurs.
Because in the end:
The true value of knowledge is not when it is easily available—but when it remains available when everything else is not.
12 Single Point of Failure Analysis
12.1 Understanding Single Points of Failure
 A single point of failure (SPOF) exists when one component within a system has the ability to bring the entire system down if it fails. These points are often hidden within otherwise functional systems, only becoming visible when disruption occurs.
A single point of failure (SPOF) exists when one component within a system has the ability to bring the entire system down if it fails. These points are often hidden within otherwise functional systems, only becoming visible when disruption occurs.
In knowledge systems, single points of failure are particularly dangerous because they concentrate risk. A system may appear robust, but if access ultimately depends on one critical element, that element becomes the defining weakness of the entire architecture.
This is not always obvious. Many systems are built with layers of redundancy at certain levels, but still rely on a single point at another level. For example, a system may have redundant storage but depend on a single access device. Or it may distribute data across servers but rely on one platform for access.
Single points of failure can exist in different forms:
- Physical (a single device or storage medium)
- Logical (a single file structure or format)
- Access-based (a single interface or platform)
- Human (a single person who understands the system)
The presence of a single point of failure does not guarantee failure. However, it guarantees that if that point fails, the system fails with it.
The objective of resilience is not to eliminate all failure, but to eliminate the ability for any single failure to cause total system loss.
12.2 Identifying Critical Failure Nodes
To understand how systems fail, it is necessary to identify the nodes within them that carry the highest level of dependency. These nodes represent the points where failure has the greatest impact.
Critical failure nodes often include:
- Central storage locations
- Primary access devices
- Software environments required for interpretation
- Network gateways or access points
In many systems, these nodes are not immediately visible because they are abstracted behind interfaces or automation. Users interact with the system as a whole, without recognizing the specific components that enable it.
For example:
- A cloud platform may appear distributed, but access depends on a single login system
- A hardware device may contain redundant storage, but access depends on the device functioning
- A document collection may exist across multiple files, but access depends on the organization of those files
Identifying these nodes requires breaking the system down into its components and asking:
- What must function for access to be possible?
- What happens if this component fails?
- Is there an alternative path to access?
If no alternative path exists, the component represents a single point of failure.
This analysis reveals not only where systems are vulnerable, but also how those vulnerabilities can be addressed.
12.3 Comparative SPOF Analysis Across Systems
Different knowledge systems exhibit different types of single points of failure. These differences are directly tied to their underlying architecture.
In online systems, the primary single point of failure is access control. Even if the infrastructure is distributed, the user interacts with a centralized platform. If access to that platform is lost, the entire system becomes unavailable.
In hardware-based systems, such as Prepper Disk™, the device itself becomes the single point of failure. All data and functionality are tied to that device. If it fails, access is lost unless an identical system is available.
In PDF collections, the single point of failure is often organizational. While the data may exist across multiple files, access depends on the ability to locate and interpret those files. If organization breaks down, usability is lost.
In physical book systems, the primary risk is physical concentration. A collection stored in one location can be lost due to environmental damage. While individual books are independent, the collection as a whole may still have a centralized vulnerability.
Prepper Offline™ reduces single points of failure by distributing both data and access. Because the system can exist across multiple devices and locations, no single component determines availability.
Across these systems:
- Online systems → access platform is the SPOF
- Hardware systems → device is the SPOF
- PDF collections → organization is the SPOF
- Physical books → location is the SPOF
- Distributed file systems → SPOF minimized through replication
This comparison highlights how architecture determines risk.
12.4 Concentration vs Distribution of Risk
The presence of a single point of failure is directly related to how risk is distributed within a system.
Concentrated systems place critical functionality into a single component. This simplifies design and operation but increases vulnerability. When that component fails, the system fails completely.
Distributed systems spread functionality across multiple components. This reduces the impact of any single failure but introduces complexity in coordination and management.
The trade-off can be summarized as:
- Concentration → simplicity, higher risk
- Distribution → resilience, increased complexity
In knowledge systems, the goal is not to eliminate complexity entirely, but to ensure that complexity does not create new failure points.
Prepper Offline™ achieves this by distributing data without introducing coordination complexity. Copies exist independently, and access does not depend on synchronization or communication between them.
In contrast, some distributed systems rely on coordination mechanisms that introduce new dependencies. If those mechanisms fail, the system may still experience disruption.
The key insight is:
Distribution reduces risk only when it does not introduce additional critical dependencies.
12.5 Lessons from Digital Wealth Systems
Digital wealth systems provide a clear example of how single points of failure can impact access.
In custodial systems, such as exchanges, the platform represents a single point of failure. Users rely on the platform for access, and if it fails or restricts access, assets become inaccessible.
In non-custodial systems, such as hardware wallets, the device or private key becomes the single point of failure. Loss or damage to that component can result in permanent loss of access.
These systems demonstrate two different types of concentration risk:
- Platform concentration → external dependency
- Device/key concentration → internal dependency
Both models highlight the importance of redundancy and distribution.
Applying these lessons to knowledge systems:
- Centralized platforms introduce external SPOFs
- Hardware-based systems introduce internal SPOFs
- Poorly organized systems introduce operational SPOFs
Prepper Offline™ addresses these risks by enabling distribution without reliance on a central authority or single device.
The parallel is clear:
Reducing single points of failure requires distributing control, not just data.
12.6 Mitigation Strategies for Single Points of Failure
Eliminating or reducing single points of failure requires intentional design and management. It is not enough to recognize vulnerabilities—systems must be structured to address them.
Effective mitigation strategies include:
- Replicating data across multiple independent locations
- Ensuring access through multiple devices
- Using standardized formats that remain compatible over time
- Simplifying interfaces to reduce reliance on specialized knowledge
These strategies focus on reducing dependency on any single component.
However, mitigation is not only technical. It also involves process and discipline. Systems must be maintained, tested, and validated regularly to ensure that redundancy remains effective.
For example:
- Backups must be accessible, not just stored
- Multiple copies must be kept current
- Access methods must be tested under real conditions
Without active management, redundancy can become ineffective over time.
The goal is to ensure that no single failure—whether physical, technical, or human—can eliminate access to knowledge.
12.7 In Summary
Single points of failure represent the most critical vulnerabilities within knowledge systems. They define how systems fail and determine whether failure results in partial disruption or total loss.
Key insights include:
- A single point of failure can exist at any layer of a system
- Concentrated systems are more vulnerable to catastrophic failure
- Distributed systems reduce risk but require careful design
- Redundancy must be independent to be effective
From a preparedness perspective, the objective is clear:
No single component should determine access to critical knowledge.
The key insight is:
A system is only as strong as its weakest point—and only as resilient as its ability to function without it.
Because in the end:
The failure that matters most is not the one that occurs—but the one that leaves you with no way to recover.
13 Redundancy & Replication Strategies
13.1 The Role of Redundancy in System Resilience
 Redundancy is one of the most fundamental principles of resilience. It is the mechanism by which systems continue to function when individual components fail. Without redundancy, failure in any critical component results in loss of access. With redundancy, failure becomes manageable.
Redundancy is one of the most fundamental principles of resilience. It is the mechanism by which systems continue to function when individual components fail. Without redundancy, failure in any critical component results in loss of access. With redundancy, failure becomes manageable.
In knowledge systems, redundancy ensures that information is not tied to a single instance. It allows for recovery, continuity, and flexibility under changing conditions.
However, not all redundancy is equal.
Some systems rely on centralized backups, which protect against data loss but do not guarantee access. Others distribute copies across independent environments, reducing both loss and access risk.
The effectiveness of redundancy depends on:
- Independence of copies
- Accessibility of backups
- Consistency across instances
- Simplicity of replication
Redundancy is not simply about having multiple copies. It is about ensuring that those copies remain usable under real-world conditions.
This distinction separates theoretical redundancy from practical resilience.
13.2 Copy-Based Redundancy: The Prepper Offline™ Advantage
Prepper Offline™ is built around a replication-first model. Instead of protecting a single system, it enables users to create multiple independent copies that can be stored across devices, locations, and environments.
This approach shifts the focus from protection to distribution.
Each copy is:
- Fully functional and self-contained
- Independent of other instances
- Accessible without synchronization or coordination
- Easily duplicated without degradation
This creates a form of redundancy that is both simple and scalable.
Users can:
- Store copies on multiple devices
- Distribute copies across different locations
- Maintain backups without complex systems
Because each instance is complete, there is no dependency between copies. Loss of one does not affect the others.
This model reduces several risks:
- No single point of failure
- No dependency on centralized backup systems
- No requirement for continuous synchronization
From a resilience perspective, this is a significant advantage. It allows redundancy to be implemented without introducing additional complexity.
The key insight is:
Redundancy is most effective when it is easy to create and maintain.
13.3 Physical Duplication: Constraints of Analog Systems
In physical systems, redundancy requires duplication of physical materials. This process is inherently more constrained than digital replication.
To achieve redundancy with physical books, users must:
- Acquire multiple copies
- Store them in different locations
- Protect them from environmental risks
This introduces limitations:
- Cost of duplication
- Storage space requirements
- Effort required to distribute materials
As a result, redundancy in physical systems is often limited. Many users rely on a single copy of critical materials, which introduces a clear vulnerability.
When duplication is implemented effectively, physical systems can be highly resilient. Multiple copies stored in separate locations provide strong protection against localized loss.
However, achieving this level of redundancy requires planning and resources.
The key distinction is:
- Physical redundancy is possible but resource-intensive
- Digital redundancy is scalable and low-cost
This difference affects how easily redundancy can be maintained over time.
13.4 Device-Level Redundancy: Hardware-Based Limitations
Hardware-centric systems, such as Prepper Disk™, rely on device-level redundancy. To protect against failure, users must maintain multiple devices with identical or similar configurations.
This introduces a different set of challenges.
Redundancy requires:
- Additional hardware devices
- Synchronization of content across devices
- Maintenance of each system
These requirements create barriers to effective redundancy:
- Higher cost compared to file-based replication
- Increased complexity in managing multiple devices
- Greater likelihood of inconsistencies between systems
In many cases, redundancy is not fully implemented. Users may have backup devices, but they are not always updated or readily accessible.
This creates a gap between theoretical and practical redundancy.
From a resilience perspective, device-level redundancy is less efficient than file-based replication. It requires more effort to achieve the same level of protection.
The key insight is:
Redundancy that depends on hardware duplication is inherently limited by cost and complexity.
13.5 Organizational Redundancy: Managing PDF Collections
PDF collections rely on organizational redundancy rather than structural redundancy. Files can be copied easily, but maintaining consistency and usability across copies requires careful management.
Redundancy in this model involves:
- Duplicating files across storage locations
- Maintaining consistent folder structures
- Ensuring that all copies are complete and up to date
This introduces several challenges:
- Version control across multiple copies
- Risk of missing or outdated files
- Difficulty maintaining consistent organization
While replication is technically simple, maintaining a usable system requires discipline and ongoing effort.
Without proper management, redundancy can become ineffective. Copies may exist, but they may not be reliable or easy to use.
This creates a distinction between:
- Data redundancy (files exist in multiple places)
- Operational redundancy (files are usable and consistent)
PDF collections often achieve the first but struggle with the second.
The key insight is:
Redundancy must preserve usability, not just data.
13.6 Network-Based Redundancy: Online System Limitations
Online systems rely on infrastructure-level redundancy. Large platforms distribute data across multiple servers and data centers to ensure availability.
From a technical perspective, this creates a highly redundant system. However, this redundancy is not controlled by the user.
User access depends on:
- Platform availability
- Network connectivity
- Account and permission status
Even if the underlying infrastructure is redundant, access remains centralized.
This creates a critical limitation:
- Redundancy exists within the system
- Access to that redundancy is not guaranteed
If the platform becomes unavailable, the user cannot access the data, regardless of how many backups exist within the system.
This contrasts with user-controlled redundancy, where copies are directly accessible.
The key distinction is:
- Infrastructure redundancy → protects the platform
- User-controlled redundancy → protects access
From a preparedness perspective, only the latter ensures continuity.
13.7 Designing Effective Redundancy Strategies
Effective redundancy requires more than duplication. It requires intentional design to ensure that copies remain accessible and usable under different conditions.
A well-designed redundancy strategy includes:
- Multiple independent copies of critical data
- Storage across different devices and locations
- Use of standardized formats for long-term compatibility
- Regular validation of access and integrity
These elements ensure that redundancy is both effective and sustainable.
It is also important to balance redundancy with simplicity. Overly complex systems can introduce new failure points, reducing overall resilience.
The goal is to create a system where:
- Failure of one component does not disrupt access
- Recovery is straightforward and reliable
- Maintenance requirements are manageable
This approach aligns with broader preparedness principles, where redundancy is used to mitigate risk rather than eliminate it entirely.
13.8 In Summary
Redundancy and replication are central to building resilient knowledge systems. They determine whether a system can continue to function when components fail.
Key insights include:
- Redundancy reduces the impact of failure
- Replication must be independent to be effective
- Simplicity improves maintainability
- User-controlled redundancy ensures access
Different systems implement redundancy in different ways:
- File-based systems enable scalable replication
- Physical systems require resource-intensive duplication
- Hardware systems depend on device-level backups
- PDF collections require organizational discipline
- Online systems rely on infrastructure-level redundancy
The key insight is:
Redundancy is not about having more copies—it is about ensuring that those copies remain accessible when they are needed.
Because in the end:
A backup that cannot be accessed is no different than no backup at all.
14 Offline Durability vs Digital Fragility
14.1 Defining Durability in Knowledge Systems
 Durability is often misunderstood in the context of knowledge systems. It is commonly assumed that if information exists, it is durable. However, durability is not defined by existence—it is defined by the ability of a system to preserve both the integrity and accessibility of information over time.
Durability is often misunderstood in the context of knowledge systems. It is commonly assumed that if information exists, it is durable. However, durability is not defined by existence—it is defined by the ability of a system to preserve both the integrity and accessibility of information over time.
A durable system must withstand not only immediate disruptions but also long-term degradation. This includes physical wear, technological change, environmental exposure, and shifts in how systems are used. Durability is therefore not a static characteristic, but a dynamic one that evolves with conditions.
In knowledge systems, durability must account for two dimensions:
- Data preservation → the information continues to exist
- Access preservation → the information remains usable
A system that preserves data but loses accessibility is not durable. Similarly, a system that allows access but degrades over time is unreliable. True durability requires both.
This distinction becomes critical when comparing offline and digital systems, as each approaches durability in fundamentally different ways.
14.2 Time as a Stress Factor
Time is one of the most significant stressors on any system. While immediate failures are often visible and dramatic, long-term degradation is gradual and often overlooked.
Over time, all systems are subject to:
- Physical wear and environmental exposure
- Technological obsolescence
- Changes in user behavior and knowledge
- Loss of supporting infrastructure
Digital systems are particularly vulnerable to time-based degradation. File formats may become obsolete, software may no longer be supported, and hardware may fail or become incompatible with newer systems.
Physical systems are also affected by time, but in different ways. Books may degrade due to environmental factors, but their format remains consistent and accessible as long as they are physically intact.
This creates a contrast:
- Digital durability depends on ongoing compatibility
- Physical durability depends on environmental protection
From a resilience perspective, time introduces uncertainty. Systems that require ongoing maintenance or adaptation are more vulnerable to long-term failure.
The key insight is:
Durability is not just about surviving today—it is about remaining functional tomorrow.
14.3 Environmental Risks (Fire, Water, EMP, Decay)
Environmental factors represent one of the most direct threats to knowledge systems. Unlike technical failures, which may be mitigated through redundancy, environmental damage can be immediate and irreversible.
Common environmental risks include:
- Fire → complete destruction of physical materials and hardware
- Water → damage to paper, electronics, and storage media
- Mold and decay → gradual degradation of physical materials
- Electromagnetic events (EMP) → potential damage to electronic devices and storage
Different systems respond to these risks in different ways.
Physical books are vulnerable to fire, water, and decay but are unaffected by electromagnetic events. Digital systems, particularly those dependent on electronic storage, are vulnerable to power-related and electromagnetic disruptions but may be protected from localized environmental damage through distribution.
This creates a layered risk profile:
- Physical systems → vulnerable to environmental exposure
- Digital systems → vulnerable to electrical and electronic disruption
- Distributed systems → reduce risk through geographic separation
The key distinction is that no system is immune to environmental risk. Each system shifts vulnerability to different types of threats.
From a preparedness perspective, durability requires not only protecting individual systems but also distributing them to reduce the impact of localized events.
14.4 Time-Based Degradation Across Systems
Different knowledge systems degrade at different rates and in different ways. Understanding these degradation patterns is essential for evaluating long-term reliability.
Physical books degrade gradually. Paper may yellow, bindings may weaken, and pages may deteriorate. However, this degradation is often visible and predictable. With proper storage conditions, books can remain usable for decades or even centuries.
Digital systems degrade less visibly but more unpredictably. Storage media may fail without warning, and file corruption may not be detected until access is attempted. Additionally, software and hardware compatibility issues can render data inaccessible even if it remains intact.
PDF collections are particularly vulnerable to organizational degradation. Over time, files may become disorganized, duplicated, or outdated, reducing usability even if the data itself remains unchanged.
Hardware-based systems introduce another form of degradation. Devices may function reliably for years but eventually fail due to wear, obsolescence, or lack of maintenance.
Distributed file-based systems, such as Prepper Offline™, mitigate some of these risks through replication. Individual instances may degrade, but the system as a whole remains functional as long as at least one copy is intact.
This creates a comparative view:
- Physical systems → slow, visible degradation
- Digital systems → hidden, unpredictable degradation
- Distributed systems → localized degradation with overall continuity
The key insight is:
Durability is influenced not only by how systems fail, but by how detectable and manageable that failure is.
14.5 Offline Stability vs Digital Volatility
Offline systems are inherently more stable because they are not subject to continuous change. Once created, they remain static unless intentionally modified. This stability reduces the number of variables that can affect system behavior over time.
Digital systems, particularly those connected to online environments, are more volatile. They are subject to:
- Software updates
- Platform changes
- Shifts in access policies
- Evolving user interfaces
While these changes can improve functionality, they also introduce risk. A system that changes frequently may become incompatible, unstable, or difficult to use under certain conditions.
This creates a trade-off:
- Stability → predictability and reliability
- Volatility → adaptability and continuous improvement
Offline systems favor stability, making them more predictable under stress. Online systems favor volatility, making them more adaptable but less reliable under disruption.
Prepper Offline™ benefits from this stability. Once deployed, the system does not change unless the user updates it. This reduces the risk of unexpected behavior.
The key insight is:
A system that does not change is easier to rely on under uncertain conditions.
14.6 Durability vs Scalability Trade-Off
Durability and scalability often exist in tension. Systems that are highly durable may be difficult to scale, while systems that scale easily may introduce additional points of fragility.
Physical books are highly durable but difficult to scale. Expanding a physical library requires additional space, resources, and effort. Distribution is limited by physical constraints.
Digital systems scale easily. Large volumes of information can be stored, duplicated, and distributed with minimal effort. However, this scalability often introduces additional dependencies, reducing overall durability.
PDF collections and distributed file-based systems occupy an intermediate position. They allow for scalable storage while maintaining a level of durability, depending on how they are managed.
Prepper Offline™ balances these factors by combining:
- Digital scalability through file-based storage
- Durability through replication and independence
This balance is a key architectural advantage. It allows the system to grow without significantly increasing fragility.
The key insight is:
The most effective systems balance durability and scalability rather than maximizing one at the expense of the other.
14.7 Comparative Durability Across Systems
When durability is evaluated across all systems, clear patterns emerge.
- Physical books offer high durability under stable environmental conditions but are vulnerable to localized damage
- Online systems offer high availability under normal conditions but low durability under disruption
- Hardware-based systems offer controlled environments but are limited by device lifespan
- PDF collections offer moderate durability but depend on organization and maintenance
- Prepper Offline™ offers high durability through replication and reduced dependency
This comparison highlights the importance of considering both short-term and long-term performance.
Durability is not determined by how a system performs under ideal conditions, but by how it maintains functionality over time and under stress.
14.8 In Summary
Durability is a critical factor in evaluating knowledge systems. It determines whether information remains accessible not only in the present, but in the future.
Key insights include:
- Durability requires both data preservation and access preservation
- Time introduces gradual and often hidden forms of degradation
- Environmental risks affect systems differently based on their architecture
- Stability improves predictability, while volatility introduces risk
- Effective systems balance durability with scalability
From a preparedness perspective, durability is not optional—it is essential.
The key insight is:
A system that cannot endure over time cannot be relied upon when it matters most.
Because in the end:
Knowledge that degrades into inaccessibility is no different than knowledge that was never preserved at all.
15 Usability Under Stress Conditions
15.1 Why Usability Matters More Than Capability
 A system’s capability is often measured by what it can do under ideal conditions. It may store vast amounts of information, provide powerful search functions, or support complex workflows. However, in real-world scenarios—especially under stress—capability becomes secondary to usability.
A system’s capability is often measured by what it can do under ideal conditions. It may store vast amounts of information, provide powerful search functions, or support complex workflows. However, in real-world scenarios—especially under stress—capability becomes secondary to usability.
Usability determines whether a system can actually deliver value when it is needed.
In preparedness contexts, stress conditions change how people interact with systems. Time pressure, fatigue, uncertainty, and environmental constraints all reduce the ability to navigate complexity. Systems that are efficient under normal conditions may become difficult or impossible to use.
This creates a critical distinction:
- Capability defines potential
- Usability defines outcome
A highly capable system that cannot be used effectively under stress provides little value. In contrast, a simpler system that remains usable under adverse conditions can be significantly more reliable.
The goal of system design is not to maximize features, but to ensure that essential functions remain accessible when conditions degrade.
15.2 Cognitive Load and Decision-Making
Cognitive load refers to the mental effort required to process information and make decisions. Under normal conditions, users can manage moderate levels of complexity. Under stress, cognitive capacity is reduced.
This reduction affects:
- Memory recall
- Attention span
- Ability to navigate unfamiliar systems
- Speed of decision-making
Systems that require multiple steps, complex navigation, or detailed knowledge introduce higher cognitive load. Under stress, these systems are more likely to fail—not because they are broken, but because they cannot be used effectively.
Different knowledge systems impose different levels of cognitive load:
- Online systems may require navigation through multiple pages and interfaces
- PDF collections require users to remember file locations and structures
- Hardware systems may require understanding of device operation
- Physical books require manual searching and interpretation
- Prepper Offline™ reduces cognitive load through structured, consistent access
The key insight is:
- High cognitive load → increased risk of user failure
- Low cognitive load → improved reliability under stress
Systems that simplify access and reduce decision points are more effective in real-world scenarios.
15.3 Speed of Retrieval vs Depth of Information
In critical situations, the speed at which information can be retrieved is often more important than the volume of information available. A system may contain extensive knowledge, but if that knowledge cannot be accessed quickly, its value is reduced.
This creates a trade-off between:
- Depth → the amount of information available
- Speed → the time required to access relevant information
Different systems handle this trade-off differently.
Online systems excel in speed under normal conditions due to advanced search capabilities. However, this advantage disappears entirely when connectivity is lost.
PDF collections may contain deep information but require manual searching across multiple documents, which can be time-consuming.
Physical books provide reliable access but require manual navigation, which can slow retrieval.
Prepper Offline™ balances these factors by providing structured navigation within a local, offline environment. This allows for relatively fast retrieval without relying on external systems.
The key insight is:
A system must provide sufficient speed of access to be useful under time constraints.
In high-pressure scenarios, delayed access can be equivalent to no access at all.
15.4 Interface Simplicity and Consistency
The interface through which users interact with a system plays a critical role in usability. A complex or inconsistent interface increases the likelihood of errors and delays, particularly under stress.
Effective interfaces share several characteristics:
- Consistency across all sections
- Clear navigation paths
- Minimal reliance on user memory
- Predictable behavior
Inconsistent systems force users to adapt continuously, increasing cognitive load and reducing efficiency.
Different systems exhibit varying levels of interface consistency:
- Online platforms may change over time due to updates
- PDF collections lack a unified interface entirely
- Hardware systems depend on the design of their internal software
- Physical books rely on standard formats but vary between publications
- Prepper Offline™ maintains a consistent, browser-based interface across all content
Consistency reduces the effort required to use a system. Once users understand how one part of the system works, they can apply that knowledge across the entire system.
The key insight is:
Consistency reduces uncertainty, and reduced uncertainty improves usability under stress.
15.5 Offline vs Online Behavior Under Stress
Stress conditions often coincide with system degradation. This is where the differences between offline and online systems become most apparent.
Online systems are highly efficient when fully operational. However, they are also highly dependent. Under stress conditions that affect connectivity or infrastructure, their usability drops to zero.
Offline systems, while sometimes less efficient under ideal conditions, maintain functionality when external dependencies fail. This creates a different usability profile:
- Online systems → high usability until failure, then none
- Offline systems → moderate usability with consistent availability
This difference is critical in preparedness scenarios. Systems that maintain consistent, if limited, usability are often more valuable than systems that provide high performance only under ideal conditions.
Prepper Offline™ exemplifies this balance. It may not match the speed or scale of online systems, but it provides stable, predictable access regardless of external conditions.
The key insight is:
Consistency of access is more important than peak performance.
15.6 Human Factors: Training, Familiarity, and Stress Response
Usability is not determined solely by system design. It is also influenced by the user’s familiarity with the system.
Under stress, people rely on:
- Habit and repetition
- Familiar workflows
- Simple, well-understood processes
Systems that require training or practice may perform well for experienced users but fail for those who are unfamiliar with them.
Different systems place different demands on users:
- Online systems rely on familiarity with navigation and search
- PDF collections require knowledge of organization and file structure
- Hardware systems require understanding of device operation
- Physical books require reading and manual navigation skills
- Prepper Offline™ benefits from familiarity with standard web interfaces
Training reduces cognitive load and improves usability. However, systems that are intuitive require less training and are more accessible to a wider range of users.
The key insight is:
A system is only as usable as the user’s ability to operate it under stress.
Preparedness systems should assume limited time for training and prioritize intuitive design.
15.7 Comparative Usability Across Systems
When usability is evaluated across all systems under stress conditions, clear patterns emerge.
- Online systems provide high usability under normal conditions but fail completely under disruption
- Hardware systems provide structured access but depend on device functionality
- PDF collections offer flexibility but require significant user effort to navigate
- Physical books provide reliable access but slower retrieval
- Prepper Offline™ provides consistent, structured access with moderate speed
This comparison highlights a key principle:
Usability is not about maximizing efficiency—it is about maintaining functionality under adverse conditions.
Systems that degrade gracefully, maintaining partial usability, are more reliable than those that fail completely.
15.8 In Summary
Usability under stress is a critical factor in evaluating knowledge systems. It determines whether information can be accessed and applied when it is needed most.
Key insights include:
- High capability does not guarantee usability
- Cognitive load increases under stress, reducing system effectiveness
- Speed of retrieval is critical in time-sensitive scenarios
- Interface consistency improves reliability
- Offline systems provide more consistent usability under disruption
From a preparedness perspective, usability is not a secondary concern—it is central to system effectiveness.
The key insight is:
A system that cannot be used under stress is functionally equivalent to a system that does not exist.
Because in the end:
The value of knowledge is not measured by how much you have—but by how much you can actually use when it matters most.
16 Ownership, Control, and Sovereignty of Knowledge
16.1 The Illusion of Ownership in Digital Systems
 In modern digital environments, ownership is often assumed but rarely examined. Users interact with systems in ways that feel like control—they can search, retrieve, and store information. However, this interaction is frequently mistaken for true ownership.
In modern digital environments, ownership is often assumed but rarely examined. Users interact with systems in ways that feel like control—they can search, retrieve, and store information. However, this interaction is frequently mistaken for true ownership.
In reality, most digital systems provide access, not control.
When knowledge is stored on external platforms, within proprietary systems, or behind authentication layers, the user does not own the information in a meaningful sense. They are granted permission to access it under specific conditions.
This creates an illusion:
- The information appears available
- The system appears reliable
- The user feels in control
But this control is conditional.
If the platform changes, restricts access, or becomes unavailable, the user’s ability to retrieve that information disappears. The knowledge may still exist, but it is no longer accessible.
This distinction is subtle but critical.
Ownership is not defined by the ability to access something today—it is defined by the ability to access it regardless of external conditions.
16.2 Defining True Ownership of Knowledge
True ownership of knowledge requires more than possession or access. It requires control over both the data and the means of accessing it.
A system that supports true ownership allows the user to:
- Store information locally
- Access it without permission or authentication
- Duplicate and distribute it freely
- Maintain access independent of external systems
This definition aligns with broader principles of sovereignty. Ownership implies that the user is not dependent on another entity to exercise control.
In knowledge systems, this means:
- The data must be physically or logically controlled by the user
- The tools required for access must be available without restriction
- The system must function without external validation
Systems that meet these criteria provide a higher level of reliability because they remove external points of control.
The key insight is:
Ownership is not about where the data is stored—it is about who controls access to it.
16.3 Control Layers: Who Actually Controls Access?
To understand ownership, it is necessary to examine the layers of control within a system. These layers determine who ultimately decides whether access is granted or denied.
In most digital systems, control exists at multiple levels:
- Platform control → who manages the system
- Infrastructure control → who operates the servers and networks
- Software control → who defines how the system functions
- User control → who interacts with the system
In online systems, control is largely external. The platform determines access, the infrastructure supports it, and the user operates within those constraints.
In hardware-based systems, control shifts partially to the user. The device is owned, but its functionality may still depend on software and internal systems.
In file-based systems, control is more fully localized. The user owns the data, the storage, and the access method.
In physical systems, control is entirely local. The user possesses the material and accesses it directly.
This creates a spectrum of control:
- External control → limited ownership
- Shared control → partial ownership
- Local control → full ownership
Understanding where a system falls on this spectrum is essential for evaluating its reliability.
16.4 Comparison to Digital Wealth: Custody vs Self-Custody
The distinction between ownership and access in knowledge systems closely parallels the difference between custodial and non-custodial models in digital wealth.
In custodial systems, assets are held by a third party. The user has access but does not control the underlying system. Access depends on the platform’s continued operation and policies.
In non-custodial systems, the user holds direct control over their assets. This removes dependency on external platforms but introduces responsibility for management and security.
Knowledge systems exhibit similar patterns:
- Online platforms → custodial access to information
- Hardware systems → controlled but device-dependent access
- File-based systems → self-custody of knowledge
- Physical systems → direct ownership
Prepper Offline™ aligns with the self-custody model. It allows users to take full control of their knowledge by storing it locally and removing dependency on external systems.
This creates a direct parallel:
- Custodial systems → convenience with dependency
- Self-custody systems → control with responsibility
The key insight is:
Control increases resilience, but also requires intentional management.
16.5 Risk of External Control and Censorship
One of the most significant risks in externally controlled systems is the potential for access to be restricted, altered, or removed. This can occur for a variety of reasons, including technical failures, policy changes, or external pressures.
In online systems, users have limited influence over:
- Content availability
- Access permissions
- Platform policies
- System continuity
This creates a vulnerability that is not always visible. Systems may function reliably for extended periods, leading users to assume that access is permanent.
However, external control introduces uncertainty.
Content can be:
- Modified or removed
- Restricted based on policy changes
- Made inaccessible due to system changes
This risk is not limited to extreme scenarios. Even minor changes in platform behavior can affect access.
Offline systems reduce this risk by removing external control. When knowledge is stored locally, access cannot be restricted by third parties.
The key insight is:
Control over access determines resistance to external interference.
16.6 Sovereignty Through Distribution
Sovereignty in knowledge systems is achieved not only through control, but through distribution. A system that is controlled locally but exists in a single instance remains vulnerable to loss.
Distribution extends control by reducing reliance on any single copy or location.
Prepper Offline™ enables this by allowing users to:
- Create multiple independent copies
- Store them across different devices and locations
- Maintain access regardless of localized failure
This creates a form of distributed ownership.
Unlike centralized systems, where control is concentrated, distributed systems allow control to exist in multiple places simultaneously.
This approach provides several advantages:
- Reduced risk of total loss
- Increased flexibility in access
- Greater resilience to localized disruptions
Sovereignty is strengthened when control is both local and distributed.
The key insight is:
True control is not just local—it is also redundant.
16.7 Strategic Implications for Preppers
For preppers, ownership and control of knowledge are not abstract concepts—they are practical requirements. In scenarios where systems fail or access is restricted, reliance on external platforms becomes a liability.
A resilient knowledge strategy must prioritize:
- Local control of critical information
- Redundancy across multiple environments
- Independence from external systems
This does not mean abandoning online systems entirely. Instead, it means using them as sources of information rather than repositories of dependency.
The combination of:
- Online systems for discovery
- Offline systems for control
creates a balanced approach.
Prepper Offline™ plays a central role in this strategy by enabling users to transition from conditional access to controlled ownership.
16.8 In Summary
Ownership, control, and sovereignty are fundamental to the reliability of knowledge systems. They determine whether information remains accessible under changing conditions.
Key insights include:
- Access does not equal ownership
- Control defines reliability
- External systems introduce dependency and risk
- Local and distributed systems provide greater resilience
From a preparedness perspective, the objective is clear:
Control over knowledge must reside with the user.
The key insight is:
A system you do not control is a system you cannot rely on.
Because in the end:
Knowledge is only truly yours when no one else can take away your ability to access it.
17 Building a Layered Knowledge System
17.1 Why No Single System Is Sufficient
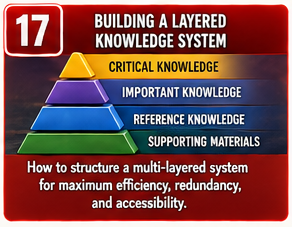 No knowledge system, regardless of how well designed, can address every risk. Each system is optimized for certain conditions and constrained by its architecture. Relying on a single system creates blind spots—areas where failure is not just possible, but likely under specific conditions.
No knowledge system, regardless of how well designed, can address every risk. Each system is optimized for certain conditions and constrained by its architecture. Relying on a single system creates blind spots—areas where failure is not just possible, but likely under specific conditions.
This is a common mistake in both digital and physical preparedness. Systems that perform well under normal conditions are often assumed to be universally reliable. However, as previous sections have shown, every system has dependencies, failure points, and limitations.
A system that is highly scalable may lack durability. A system that is highly durable may lack accessibility. A system that is simple may lack depth. These trade-offs are unavoidable.
This leads to a fundamental principle:
No single system can provide complete resilience.
Instead of searching for a perfect solution, the focus must shift to combining systems in a way that balances strengths and weaknesses. This is the foundation of a layered approach.
17.2 The Layered Model: Complementary Strengths
A layered knowledge system is built by combining multiple systems, each serving a specific role. Rather than competing with each other, these systems complement one another, creating a more resilient overall structure.
Each layer addresses a different aspect of risk:
- Online systems provide scale, updates, and discovery
- Distributed offline systems provide control and accessibility
- Physical systems provide independence and durability
This creates a structure where:
- One layer compensates for the weaknesses of another
- No single failure results in total loss of access
- Information remains available under a wider range of conditions
The effectiveness of this model depends on clear separation of roles. Each system should be used for what it does best, rather than forcing one system to serve all purposes.
The key insight is:
Resilience is achieved through combination, not substitution.
17.3 Layer 1: Online Systems for Discovery and Expansion
Online systems serve as the entry point for knowledge acquisition. They provide access to vast amounts of information, advanced search capabilities, and continuously updated content.
Platforms such as Prepping Communities exemplify this layer by offering:
- A full catalog of structured preparedness content
- Searchable postings and categorized information
- Continuous updates and expansion of knowledge
This layer is optimized for:
- Research and learning
- Discovering new information
- Accessing current and evolving content
However, it is not designed for resilience. Its dependency on infrastructure and external control makes it vulnerable under disruption.
The role of this layer is not to store critical knowledge, but to provide access to it under normal conditions.
The key insight is:
Online systems are best used for acquisition, not dependency.
17.4 Layer 2: Prepper Offline™ as the Core Resilient Layer
The second layer serves as the foundation of the knowledge system. This is where critical information is stored in a form that remains accessible under adverse conditions.
Prepper Offline™ fulfills this role by providing:
- A complete, self-contained knowledge library
- Local, browser-based access without external dependencies
- Replication across multiple devices and locations
This layer is optimized for:
- Reliable access under disruption
- Redundancy through distribution
- Consistent usability across environments
Unlike online systems, this layer does not depend on continuous operation of external infrastructure. It provides a stable, predictable access point for critical information.
An important architectural advantage is that the content available online through Prepping Communities is fully replicated within Prepper Offline™. This creates a seamless transition:
- Users can explore and evaluate content online
- The same content becomes available offline for resilient access
This linkage ensures that the offline system is not a reduced subset, but a complete extension of the online knowledge base.
The key insight is:
The core layer must be independent, replicable, and always accessible.
17.5 Layer 3: Physical Systems as the Final Fallback
The third layer consists of physical knowledge systems, primarily books and printed materials. This layer provides a level of independence that digital systems cannot fully replicate.
Physical systems are optimized for:
- Operation without power or electronic devices
- Long-term durability under stable conditions
- Guaranteed access as long as materials are physically available
This layer serves as a fallback when digital systems are unavailable. While it may lack the speed and scalability of digital systems, it provides a baseline level of reliability.
The limitations of physical systems include:
- Limited storage capacity
- Slower retrieval of information
- Difficulty in duplication and distribution
Despite these limitations, physical systems play a critical role in ensuring continuity under extreme conditions.
The key insight is:
The final layer must function independently of all digital systems.
17.6 Integration Strategy: How the Layers Work Together
The effectiveness of a layered system depends on how well the layers are integrated. Each layer must support the others without introducing unnecessary complexity.
A practical integration strategy includes:
- Using online systems to discover and evaluate information
- Transferring critical knowledge into the offline layer
- Maintaining physical backups of essential information
This creates a flow of knowledge:
- Online → discovery and expansion
- Offline → control and accessibility
- Physical → durability and independence
Each layer reinforces the others.
If online access is lost, the offline layer maintains functionality. If digital systems fail entirely, the physical layer provides continuity.
This approach ensures that no single failure disrupts access to critical knowledge.
The key insight is:
Integration is not about combining systems—it is about aligning their roles.
17.7 Risk Reduction Through Layering
Layering reduces risk by distributing it across multiple systems. Instead of relying on a single point of access, the system provides multiple paths to the same information.
This reduces:
- Dependency on any single system
- Impact of localized failures
- Risk of total access loss
Different types of risk are addressed by different layers:
- Infrastructure risk → mitigated by offline systems
- Device risk → mitigated by replication
- Environmental risk → mitigated by distribution and physical backups
By spreading risk across layers, the system becomes more resilient to a wide range of failure scenarios.
The key insight is:
Risk is not eliminated—it is distributed and managed.
17.8 In Summary
A layered knowledge system combines multiple approaches to achieve resilience. No single system provides complete protection, but together they create a robust structure.
Key insights include:
- Each system has strengths and limitations
- Combining systems reduces overall vulnerability
- Clear roles improve effectiveness
- Integration ensures continuity across layers
From a preparedness perspective, the objective is to build a system that continues to function under a wide range of conditions.
The key insight is:
Resilience is not built on a single system—it is built on how systems work together.
Because in the end:
The most reliable knowledge system is not the one that works best when everything is functioning—but the one that still works when everything else does not.
18 “Digital Wealth Is Not Permanent Wealth — It Is Conditional Access”
18.1 Reframing Wealth in the Digital Age
 The concept of wealth has evolved significantly in the digital era. Traditionally, wealth was tied to physical assets—land, gold, tools, and tangible goods. Ownership was direct, visible, and largely independent of external systems.
The concept of wealth has evolved significantly in the digital era. Traditionally, wealth was tied to physical assets—land, gold, tools, and tangible goods. Ownership was direct, visible, and largely independent of external systems.
Digital systems have changed this relationship.
Today, a significant portion of wealth exists in abstract form:
- Bank balances
- Investment accounts
- Cryptocurrencies
- Digital assets
These forms of wealth are not held physically. They exist within systems—networks, databases, and platforms—that must remain operational for access to be possible.
This creates a fundamental shift:
Wealth is no longer defined solely by what you have, but by your ability to access it.
This distinction introduces a new dimension of risk. Ownership becomes conditional, dependent on the continued operation of systems that are outside of direct control.
The same principle applies to knowledge.
Just as digital wealth depends on systems for access, digital knowledge depends on systems for retrieval. The value of both is not inherent—it is conditional.
18.2 Conditional Access: The Hidden Dependency
Conditional access is the defining characteristic of modern digital systems. It refers to the requirement that certain conditions must be met for access to be granted.
In digital wealth systems, access may depend on:
- Network connectivity
- Software compatibility
- Authentication credentials
- Platform availability
If any of these conditions fail, access is interrupted.
This dependency is often invisible during normal operation. Systems function reliably, creating the impression that access is guaranteed. However, this reliability is contingent on continuous system functionality.
The same applies to knowledge systems.
Access to information may depend on:
- Internet connectivity
- Platform availability
- Device functionality
- Software compatibility
When these conditions are met, access appears seamless. When they are not, access disappears.
The key insight is:
Digital systems do not eliminate dependency—they obscure it.
18.3 Parallel Between Digital Wealth and Knowledge Systems
The structural similarities between digital wealth and digital knowledge systems are significant. Both rely on layered architectures, both depend on external systems, and both exhibit similar failure patterns.
In both cases:
- The asset exists within a system
- Access depends on system functionality
- Control may be external or shared
- Failure results in loss of access, not necessarily loss of the asset
This creates a direct parallel:
- Digital wealth → value stored in systems
- Digital knowledge → information stored in systems
In both domains, the critical question is not:
- “Does it exist?”
But:
- “Can I access it when I need it?”
This parallel reinforces the importance of treating knowledge with the same level of scrutiny as wealth.
Both require:
- Control over access
- Reduction of dependency
- Redundancy to mitigate failure
The key insight is:
The architecture that defines access to wealth also defines access to knowledge.
18.4 Failure Conditions: When Access Becomes Zero
Digital systems often operate on a binary model of access:
- Fully accessible
- Completely inaccessible
There is rarely a gradual decline. When dependencies fail, access is lost entirely.
In digital wealth systems, this can occur when:
- Networks are unavailable
- Credentials are lost or invalid
- Platforms restrict access
- Systems experience failure
In knowledge systems, similar conditions apply:
- Loss of connectivity prevents access to online content
- Device failure prevents access to stored data
- Software incompatibility prevents interpretation of files
In each case, the asset remains in existence, but its value becomes effectively zero because it cannot be accessed.
This is a critical realization.
Value is not inherent in the asset—it is realized through access.
The key insight is:
An inaccessible asset has no practical value, regardless of its theoretical worth.
18.5 The Illusion of Permanence
One of the most pervasive assumptions in digital systems is the idea of permanence. Because digital data can be copied, stored, and backed up, it is often perceived as durable and reliable.
However, this perception overlooks the conditions required for access.
Digital systems are not inherently permanent. They are conditionally persistent.
Their persistence depends on:
- Continued compatibility of hardware and software
- Maintenance of supporting infrastructure
- Availability of access mechanisms
Without these conditions, data may remain stored but become inaccessible.
This creates an illusion:
- Data appears permanent
- Access appears guaranteed
In reality:
- Both are conditional
This illusion is reinforced by the reliability of systems under normal conditions. Users rarely encounter failure, leading to overconfidence in system stability.
The key insight is:
Permanence in digital systems is not guaranteed—it is maintained.
18.6 Breaking the Dependency: From Conditional to Controlled Access
The transition from conditional access to controlled access is the foundation of resilience.
Controlled access removes reliance on external systems and places responsibility with the user. It ensures that access is determined by local conditions rather than external factors.
In knowledge systems, this transition is achieved through:
- Local storage of information
- Use of standardized, widely supported formats
- Replication across multiple environments
- Elimination of external authentication requirements
Prepper Offline™ exemplifies this model by allowing users to:
- Store the entire knowledge base locally
- Access it without network dependency
- Replicate it across multiple devices and locations
This reduces the number of conditions required for access.
Instead of relying on multiple external systems, access depends on:
- Availability of a device
- Presence of the stored files
This simplifies the system and increases reliability.
The key insight is:
Control reduces dependency, and reduced dependency increases resilience.
18.7 Strategic Implications for Preppers
For preppers, the implications of conditional access are significant. Systems that appear reliable under normal conditions may fail when they are needed most.
A resilient strategy must account for:
- Loss of infrastructure
- Failure of devices
- Restrictions on access
- Changes in system behavior
This requires a shift in thinking:
- From access → to control
- From convenience → to reliability
- From centralization → to distribution
Knowledge systems must be designed with these principles in mind.
This includes:
- Maintaining local copies of critical information
- Reducing reliance on external platforms
- Ensuring multiple paths to access
The goal is not to eliminate digital systems, but to use them in a way that does not create dependency.
18.8 In Summary
Digital wealth and digital knowledge share a fundamental characteristic:
They are not inherently secure—they are conditionally accessible.
Key insights include:
- Digital assets depend on system functionality
- Access is determined by external and internal conditions
- Failure results in loss of access, not necessarily loss of the asset
- Control over access is more important than the existence of the asset
From a preparedness perspective, the objective is clear:
Access must be controlled, not assumed.
The key insight is:
Digital wealth is not permanent wealth—it is conditional access.
Because in the end:
What you truly own is not what exists in a system—but what you can still access when that system is gone.
19 Final Doctrine — Knowledge Resilience Principles
19.1 From Theory to Doctrine
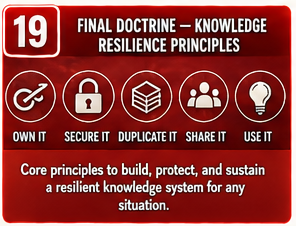 Throughout this document, we have examined knowledge systems from multiple perspectives: architecture, dependency, failure scenarios, durability, usability, and control. Each section has revealed a different aspect of how systems behave under both normal and adverse conditions.
Throughout this document, we have examined knowledge systems from multiple perspectives: architecture, dependency, failure scenarios, durability, usability, and control. Each section has revealed a different aspect of how systems behave under both normal and adverse conditions.
However, analysis alone is not sufficient.
For knowledge to be useful in preparedness, it must be translated into doctrine—clear, actionable principles that guide decisions and behavior. Doctrine simplifies complexity. It reduces a wide range of variables into a set of core rules that can be applied consistently.
In high-stress environments, there is no time to revisit theory. Decisions must be made quickly, often with incomplete information. Doctrine provides a framework for those decisions.
This section defines the core principles of knowledge resilience, based on the insights developed throughout the document.
19.2 Principle 1: Access Defines Value
The most fundamental principle is that access determines value. Information that cannot be accessed when needed has no practical utility, regardless of how comprehensive or accurate it may be.
This applies across all systems:
- Online platforms may contain vast knowledge but fail under disruption
- Local systems may store information but fail if access mechanisms are complex or unavailable
- Physical systems may remain intact but require time to navigate
The critical question is not how much information exists, but whether it can be retrieved and used under real conditions.
This principle reframes how knowledge systems are evaluated. Instead of focusing on storage capacity or features, the focus shifts to accessibility.
The key insight is:
Information is only as valuable as your ability to access it when it matters most.
19.3 Principle 2: Reduce Dependency Wherever Possible
Every dependency introduces a potential failure point. Systems that rely on multiple external conditions are more vulnerable than those that operate independently.
Dependencies can include:
- Power
- Hardware
- Software
- Network connectivity
- External platforms
While it is not possible to eliminate all dependencies, it is possible to reduce them.
Reducing dependency involves:
- Removing reliance on external systems
- Using standardized and widely supported tools
- Simplifying system architecture
Prepper Offline™ demonstrates this principle by minimizing dependency to the most basic components required for access.
The key insight is:
The fewer conditions required for access, the more reliable that access becomes.
19.4 Principle 3: Eliminate Single Points of Failure
Single points of failure represent the most critical vulnerabilities in any system. When a single component determines access, its failure results in total system loss.
Eliminating single points of failure requires:
- Distributing data across multiple instances
- Ensuring access through multiple devices
- Avoiding reliance on a single platform or location
This principle applies to both digital and physical systems.
A system that appears redundant may still contain hidden single points of failure. Identifying and addressing these points is essential for resilience.
The key insight is:
No single component should determine access to critical knowledge.
19.5 Principle 4: Replicate, Don’t Just Backup
Backups are often misunderstood as a form of redundancy. While they protect against data loss, they do not always ensure access.
Replication, in contrast, creates independent copies that are immediately usable. Each copy functions as a complete system, not just a stored backup.
Effective replication involves:
- Creating multiple complete copies
- Storing them in different locations
- Ensuring each copy is accessible without additional steps
Prepper Offline™ enables this model by allowing users to duplicate the entire system easily.
The distinction is critical:
- Backup → protects data
- Replication → preserves access
The key insight is:
A backup that cannot be quickly accessed does not provide resilience.
19.6 Principle 5: Prioritize Usability Under Stress
A system that cannot be used under stress is effectively unusable. Complexity, inconsistent interfaces, and high cognitive load reduce the likelihood that a system will function when needed.
Usability must account for:
- Time pressure
- Reduced cognitive capacity
- Limited familiarity
- Environmental constraints
Systems should be:
- Simple to navigate
- Consistent in structure
- Predictable in behavior
This principle emphasizes practical usability over theoretical capability.
The key insight is:
The best system is not the most advanced—it is the one you can use when it matters.
19.7 Principle 6: Combine Systems Into Layers
No single system provides complete protection. Each system has strengths and weaknesses, and resilience is achieved by combining them into a layered structure.
A layered knowledge system includes:
- Online systems for discovery and expansion
- Offline systems for control and accessibility
- Physical systems for durability and independence
Each layer supports the others.
If one layer fails, the others maintain continuity. This reduces the risk of total system failure.
The key insight is:
Resilience is built through combination, not reliance.
19.8 Principle 7: Control Your Access
Control is the foundation of reliability. Systems that are controlled externally introduce uncertainty, while systems that are controlled locally provide predictability.
Controlling access involves:
- Storing knowledge locally
- Removing reliance on external permissions
- Ensuring that access mechanisms are always available
This principle aligns directly with the concept of sovereignty.
Ownership is not defined by possession—it is defined by control.
The key insight is:
If you do not control access, you do not control the system.
19.9 Principle 8: Plan for Failure, Not Perfection
Systems should not be designed based on ideal conditions. They should be designed with the expectation that failure will occur.
Planning for failure involves:
- Identifying likely failure scenarios
- Ensuring that systems can continue to function under those scenarios
- Accepting that no system is immune to disruption
This mindset shifts the focus from preventing failure to managing it.
The key insight is:
Resilient systems are not those that never fail, but those that continue to function when failure occurs.
19.10 Principle 9: Treat Knowledge as Stored Wealth
In traditional preparedness, wealth is not left exposed or assumed to be accessible when needed. It is stored, protected, and distributed to ensure availability under uncertain conditions.
The same principle must be applied to knowledge.
Modern systems encourage a different mindset. Information is treated as something that can always be retrieved—searched, streamed, or accessed on demand. This creates dependency and reduces long-term resilience.
A more effective approach is to treat knowledge as a form of stored wealth.
This means:
- Acquiring knowledge intentionally rather than passively
- Storing it in controlled, local environments
- Protecting it through redundancy and replication
- Distributing it across multiple access points
This transforms knowledge from a temporary resource into a durable asset.
Just as financial wealth is:
- Earned
- Stored
- Protected
- Diversified
Knowledge must be:
- Learned or acquired
- Stored locally
- Replicated for resilience
- Distributed to reduce risk
This alignment is not conceptual—it is practical.
A person who relies on accessing knowledge externally is exposed to the same risks as someone who relies entirely on external financial systems. In both cases, access is conditional.
Prepper Offline™ is built around this principle. It enables users to convert externally accessed knowledge into locally controlled knowledge—effectively turning information into a stored asset.
The key insight is:
Knowledge should not be something you depend on accessing—it should be something you already have.
19.11 Summary
Knowledge is one of the most critical assets in preparedness. It enables decision-making, supports action, and provides the foundation for survival.
However, knowledge is only valuable if it is accessible.
Modern systems have made knowledge more abundant than ever, but they have also introduced new forms of fragility. Access is often conditional, dependent on systems that may not be available when needed.
This document has shown that resilience is not about eliminating technology, but about using it wisely—reducing dependency, increasing control, and ensuring continuity.
The final insight is simple:
Knowledge is not what you can access today—it is what you can still access when everything else fails.
Because in the end:
The difference between being prepared and being vulnerable is not what you have—it is what you can still use.
20 Implementation Guide — From Concept to Deployment
20.1 Moving from Understanding to Action
 Understanding knowledge resilience is only the first step. The value of this framework is realized only when it is applied. Without implementation, even the most well-designed systems remain theoretical.
Understanding knowledge resilience is only the first step. The value of this framework is realized only when it is applied. Without implementation, even the most well-designed systems remain theoretical.
This section provides a structured approach to moving from concept to deployment. It focuses on practical steps that translate the principles outlined in this document into a functional, resilient knowledge system.
At its core, this process requires a shift in how knowledge is perceived.
Most people treat knowledge as something they can access when needed. It is viewed as external, abundant, and always available. However, as this document has demonstrated, access to knowledge is conditional.
A more resilient approach is to treat knowledge the same way one would treat wealth.
Just as financial assets are:
- Earned
- Stored
- Protected
- Distributed
Knowledge must be:
- Acquired intentionally
- Stored locally
- Protected through redundancy
- Distributed across multiple access points
This reframes knowledge from a passive resource into an active asset.
In this model, knowledge is not something you look up—it is something you own, maintain, and secure.
This principle forms one of the foundational concepts behind Prepper Offline™. The system is designed not simply to provide information, but to allow users to store knowledge as a form of preparedness wealth, independent of external systems.
Implementation does not require perfection. It requires progress.
Most users already have some form of knowledge system in place—whether it is reliance on online platforms, scattered PDF collections, or a small set of physical books. The objective is not to replace these systems entirely, but to organize and strengthen them.
The process begins by evaluating current dependencies and identifying gaps.
20.2 Step 1: Assess Your Current Knowledge Dependencies
The first step is to understand how knowledge is currently accessed. This involves identifying where information is stored and what conditions are required to retrieve it.
Most users rely heavily on online systems without realizing the extent of that dependency.
Assessment should include:
- What information do you rely on most frequently?
- Where is that information stored?
- What systems are required to access it?
- What happens if those systems are unavailable?
This process reveals critical vulnerabilities.
For example:
- Reliance on search engines for essential knowledge
- Dependence on a single device or storage location
- Lack of offline access to critical information
The goal is to identify points where access could be lost.
The key insight is:
You cannot reduce dependency until you understand where it exists.
20.3 Step 2: Identify Critical Knowledge Categories
Not all information carries the same level of importance. Some knowledge is essential for immediate decision-making, while other information is useful but not critical.
Implementation requires prioritization.
Critical knowledge categories may include:
- Water purification and storage
- Medical and first aid procedures
- Food preparation and preservation
- Shelter and environmental protection
- Security and situational awareness
These categories represent information that must remain accessible under all conditions.
Secondary knowledge can remain in less resilient systems, but critical knowledge should be moved into controlled environments.
This step ensures that effort is focused where it matters most.
The key insight is:
Resilience begins with prioritizing what cannot be lost.
20.4 Step 3: Establish Your Core Offline Layer (Prepper Offline™)
The core of a resilient knowledge system is a reliable offline layer. This layer must provide consistent access to critical information without reliance on external systems.
Prepper Offline™ is designed to fulfill this role.
Implementation involves:
- Acquiring the Prepper Offline™ system
- Deploying it on at least one primary device
- Verifying that all content is accessible locally
At this stage, the focus is not on redundancy, but on establishing a functional baseline.
Once deployed, the system should be tested:
- Can you access content without internet connectivity?
- Is navigation clear and consistent?
- Can you locate critical information quickly?
This ensures that the system is not only present, but usable.
The key insight is:
The core layer must be operational before it can be replicated.
20.5 Step 4: Implement Replication and Distribution
Once the core system is in place, the next step is to eliminate single points of failure through replication.
This involves creating multiple independent copies of the system and distributing them across different environments.
Replication strategies include:
- Storing copies on multiple devices (laptop, external drive, USB)
- Placing copies in different physical locations
- Maintaining both primary and secondary access points
Each copy should be:
- Complete and fully functional
- Independently accessible
- Stored in a way that protects against localized risk
This step transforms the system from a single instance into a distributed network of access points.
The key insight is:
A system becomes resilient when no single loss can eliminate access.
20.6 Step 5: Integrate Physical Backup Materials
Digital systems provide flexibility and scalability, but they are not completely independent of infrastructure. Physical materials provide an additional layer of resilience.
Implementation should include:
- Selecting key reference books for critical categories
- Storing them in accessible and protected locations
- Ensuring that essential information exists in physical form
Physical materials should focus on:
- Core survival knowledge
- High-priority reference information
- Procedures that must be accessible without devices
This layer serves as a fallback when digital systems are unavailable.
The key insight is:
Physical systems provide continuity when digital systems cannot.
20.7 Step 6: Maintain and Validate the System
A knowledge system is not static. It must be maintained to ensure that it remains functional over time.
Maintenance includes:
- Updating content within the offline system
- Verifying that all copies remain intact and accessible
- Testing access under different conditions (offline, different devices)
Validation is critical.
A system that has not been tested may fail when needed. Regular checks ensure that:
- Files are not corrupted
- Devices are functional
- Access methods are still effective
This step ensures that redundancy remains meaningful.
The key insight is:
A system is only reliable if it is regularly verified.
20.8 Step 7: Train for Real-World Use
Even the most well-designed system can fail if the user is not familiar with it. Training reduces cognitive load and improves usability under stress.
Training should include:
- Navigating the system without relying on search
- Locating critical information quickly
- Using the system under simulated stress conditions
This builds familiarity and confidence.
Users should be able to:
- Access key information without hesitation
- Operate the system without external guidance
- Adapt to different devices or environments
Training transforms the system from a tool into a reliable resource.
The key insight is:
Familiarity turns access into action.
20.9 Putting It All Together
When these steps are combined, they form a complete implementation strategy:
- Assess dependencies
- Prioritize critical knowledge
- Establish a core offline system
- Replicate and distribute copies
- Integrate physical backups
- Maintain and validate regularly
- Train for real-world use
Each step builds on the previous one, creating a system that is both resilient and practical.
This approach does not require advanced technical knowledge. It relies on applying simple principles consistently.
The result is a system that:
- Reduces dependency
- Eliminates single points of failure
- Maintains access under a wide range of conditions
20.10 In Summary
Implementation is where resilience becomes real. It transforms principles into systems that can be relied upon under stress.
Key insights include:
- Understanding must lead to action
- Critical knowledge must be prioritized
- Redundancy must be intentional
- Systems must be tested and maintained
From a preparedness perspective, the objective is not to build a perfect system, but to build one that works when needed.
The key insight is:
Resilience is not achieved through design alone—it is achieved through execution.
Because in the end:
The difference between knowing and being prepared is what you actually put in place before you need it.
Appendix A: Comparison Table (Full Breakdown)
- Expanded Feature Matrix
- Risk Scoring per Solution
- Failure Mode Summary
© Prepping Communities. This content is for informational purposes only and not professional advice. Use at your own risk.
Terms | Privacy | Guidelines

